Your email account is the digital counterpart of your home address. It allows you to communicate with family, friends, and coworkers. You give it to people and businesses so they can send you the information and products you need.
Email addresses have evolved into much more than just a way to send and receive messages. You’re effectively using your email address as proof of your
How Severe is Email Hacking?
Email hacking is indeed a serious crime.
The hacking of former Alaska Governor Sarah Palin’s email account demonstrates how dangerous hacking into someone else’s email account is. This case serves as an excellent illustration of the law in this area.
David Kernell hacked Palin’s personal Yahoo email account in 2010. He was tried and sentenced to one year and one day in federal prison. He was charged with the following crimes:
Email hacking through wire fraud
Wire fraud happens when someone uses a computer, radio, television, or telephone to deceive or trick someone into giving them money, property, or information.
Stealing money is the most common type of wire fraud, but stealing personal and confidential information is also considered wire fraud. One of the most important aspects of wire fraud is that emails,
Identity theft for email hacking
Palin’s email account became her own, unique address when she created it, and no one else could use it. Kernell illegally acquired access to personal information and credentials. He changed Palin’s password so he could use the account to derail Palin’s campaign.
Online villains typically use phishing scams to hack emails
Cybersecurity company PurpleSec found that email phishing is the most common way of starting a social engineering attack. As a result, threat actors deliver malware via email nearly 92% of the time.
The company’s study also revealed that in 2018, phishing and social engineering assaults affected 62% of enterprises, with a new firm falling victim to ransomware every 14 seconds in 2019. The total number of
Why is Email Security Important?
Phishing attacks are the first steps to email hacking. Email is a prime target for cyber attacks due to vulnerabilities caused by human error that attackers can easily exploit.
Phishing emails continue to become widespread. The Covid-19 pandemic is facilitating attacks with the help of more clever social engineering tactics. Email attacks benefit cybercriminals significantly with financial gain or other crimes that they can inflict on unsuspecting victims. You never know what they can do with stolen credentials.
What cybercriminals can do with a hacked email
Your email inbox contains a wealth of information about your personal, financial, and professional life. Once a hacker knows your email credentials, all this information could be at risk. Here are what cybercriminals can do with a hacked email account:
Steal your identity
If cyber thieves gain access to your email account and search through your inbox, they may be able to gather enough information about you to steal your

Send you phishing emails
Cybercriminals can use your email address to bombard you with phishing emails in the hope of fooling you to take action. Scammers can also trick you into logging in to a fake website to steal your login credentials.
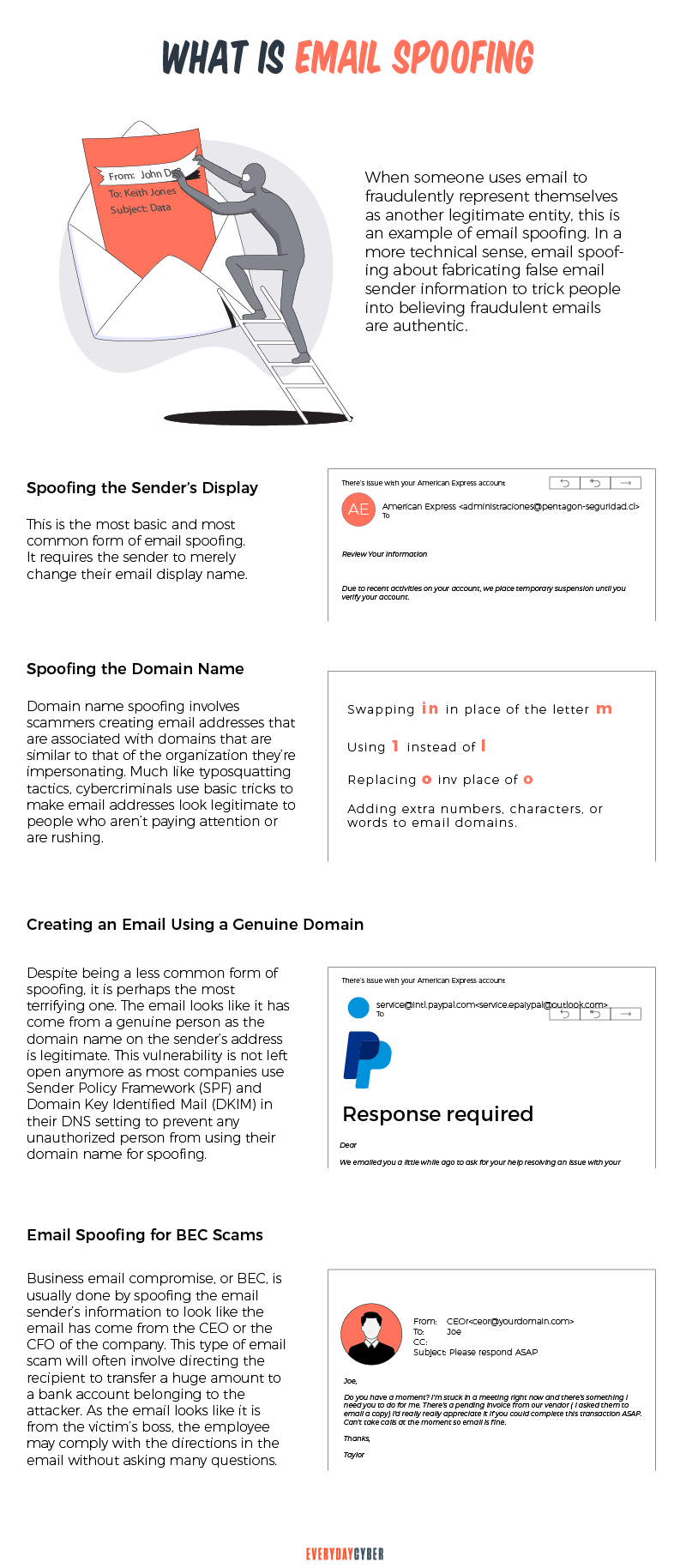
Spoof your email address
Attackers can impersonate your email address to con other people, in addition to sending fraudulent emails to your account.
This is how they go about it. They start by creating a forged sender address that looks exactly like yours, with very subtle changes like adding a period or replacing a number with a letter. They then use the email address to send spoof messages carrying harmful viruses or money requests.
Email spoofing allows scammers to avoid spam filters on most email accounts because the email address appears authentic.
Scam your contacts
Things can get even more serious if criminals are able to learn your email password. They can access your account and send email blasts to anyone on your list of contacts. These emails may contain spyware, requests for money or access to online accounts, or promotions for bogus goods or services.
Hack your other online accounts
Hackers can learn the passwords to all of your online accounts that use your email address as the username by logging in to your email account with your password.
They then simply click the “forgot password” button and change your existing password to learn the password to your other accounts that use your email address as the username. That’s why it’s critical to enable two-factor authentication for your online accounts.
Play blackmail on you
Hackers can use your hacked email account to spy on you and review your most personal emails, the sort you wouldn’t want to share publicly. If hackers find highly sensitive personal information in your inbox, they could use it to threaten or blackmail you.
By entering your email address you agree to receive emails from EveryDayCyber. We'll respect your privacy and you can unsubscribe at any time.
How Can Your Email be Hacked?
Email accounts are hacked everyday. They can be used for just about anything by cybercriminals. Email hackers use various ways to compromise or illegally access emails, but they carry out their illicit trade with these common methods:
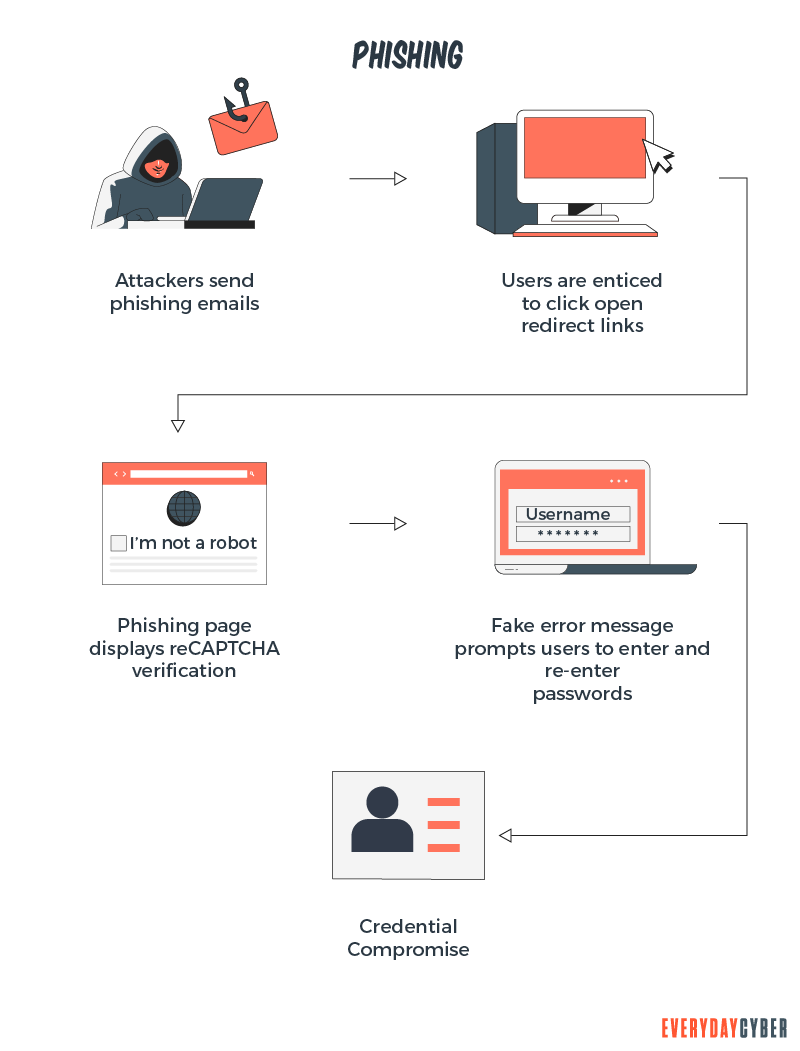
Phishing attacks
Phishing tactics are the most typical ways for email to be hacked. Phishing is the most extensively used approach because it’s easy to implement, inexpensive, and targets the weakest link in any
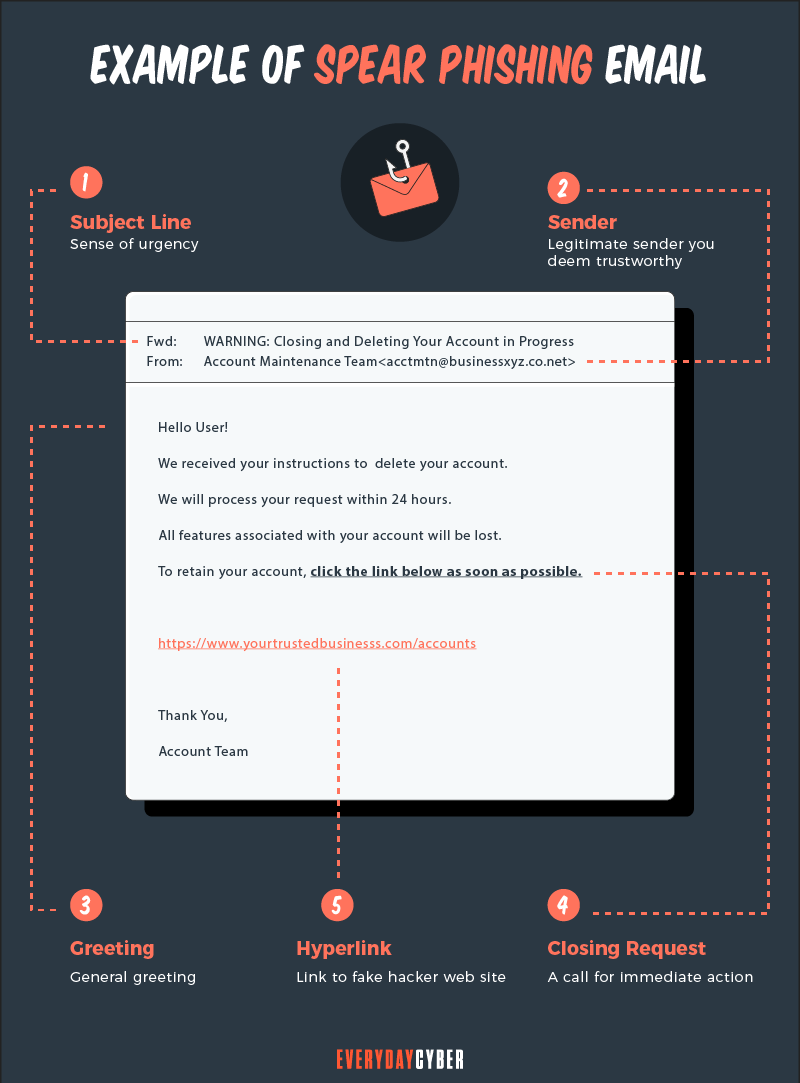
Phishing is typically carried out by sending a legitimate-looking email that directs the receiver to a false website where they are asked to enter credentials to “check” information, which is then stolen. The emails may also instruct the receiver to click a link or download something that appears to be normal but is actually harmful software.
Man in the Middle Attacks (MITMs)
In an Man in the Middle attack, an attacker intercepts data, such as a password, sent between two parties. Attackers also exploit unencrypted emails to intercept data.
MITM attacks are common on unsecured public Wi-Fi networks and evil twin Wi-Fi hotspots. Evil twin hotspots mimic the appearance of a legitimate hotspot provider, such as a coffee shop, airport lounge, or hotel. Any data sent through that hotspot can be easily intercepted.
Brute force attacks
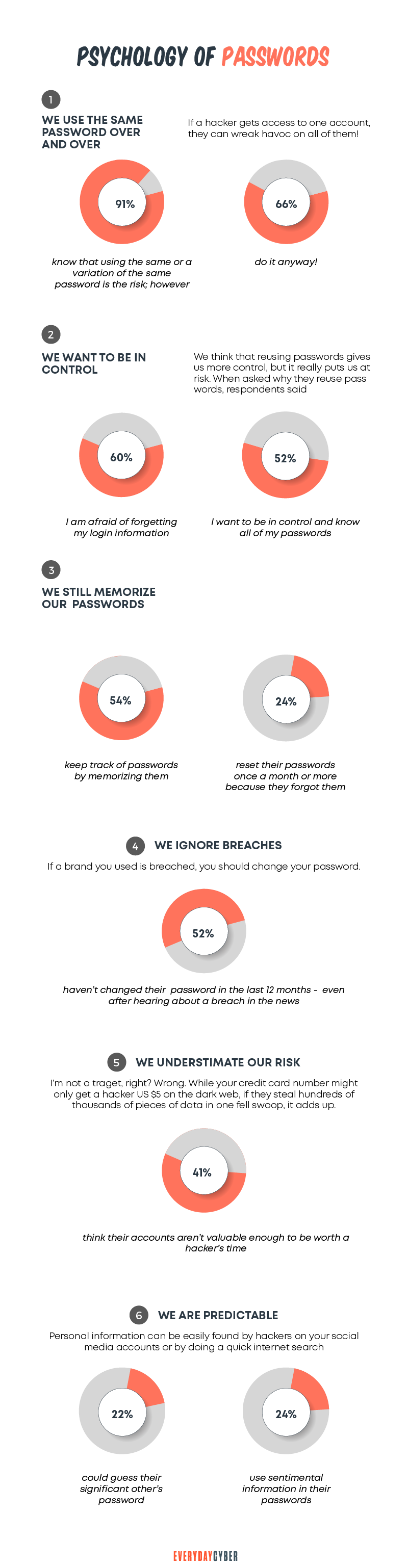
An attacker can also try to guess a user’s password as an alternative to compromising business email accounts. This is an automated method that can take thousands of attempts to guess the password. Weak password choices and failure to change default passwords make it easy for crooks to carry out this technique.
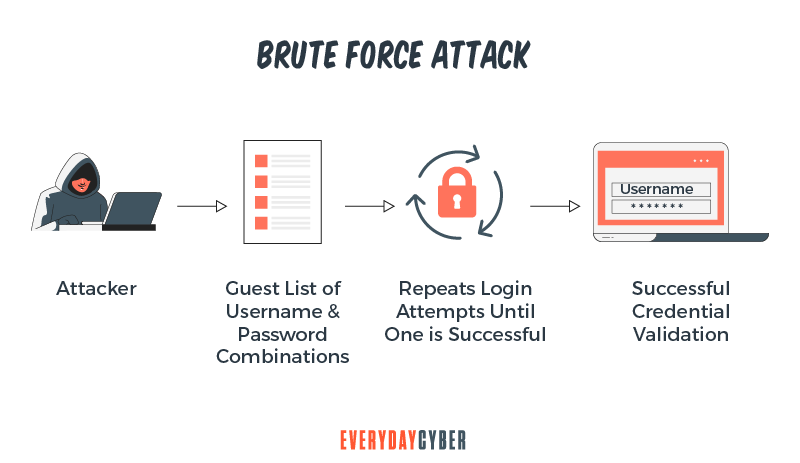
Passwords stolen in prior breaches can also be used, catching users who reuse passwords across various platforms. Brute force attackers exploit information about a person found on social media, such as a partner’s name, child’s name, pet’s name, or dates of birth, to guess passwords.
Noting down passwords on paper
Strong passwords are long and difficult to remember. As a result, some people scribble their passwords on post-it notes, tape them to their computers, or place them under their keyboard where any visitor could find them.
How to Tell If Your Email is Hacked
Being vigilant about unusual activity on your email account is key to knowing whether you’ve been hacked. Email thieves are getting smarter and more discreet in their moves such that they are now able to hide their footprint to mask suspicious activity that would give you a clue on the intrusion.
So yes, you’ll need a lot of alertness and diligence to spot signs that your email account is in danger. Let’s take a look at the most common warning signals:
You can’t log in to your email account
When you open your email, you discover that your username and password have been denied. You try again, confident that you’re using the correct password, but with no luck.
It’s possible that a hacker has obtained your password, signed in, and then changed it, shutting you out and giving them control of your account. This is the clearest sign that your email has been hacked.
A different location and IP address are used to access your mailbox
If an illegal third party gains access to your email account, they may not want to raise suspicion by changing your password. Instead, they may just monitor your incoming and outgoing messages in order to obtain additional information.
You may be able to access that information if your email provider keeps access logs. Open your mail.com account and go to Home > Manage Sessions to find out who is currently logged into your account. If the location is in a different city or country than the one you’re in, you can manually cancel the session by clicking the trash sign on the right.
You can also contact your provider and request information on which IP addresses have recently accessed your mailbox. You may soon discover if someone might be tampering with your account.
You find strange messages you didn’t send
Cybercriminals may try to commandeer your account rather than taking control and locking it completely. This allows them to send spam or collect additional information about you while remaining undetected.
People rarely check their “Sent” folder, so if someone sends messages from your mailbox, it will take much longer for you to learn of the strange messages, especially if no one responds.
If the messages are unusual, you may earn the ire of your family, friends, and other close contacts who surely know the type of content you send to them.
You receive password reset instructions
Another clue that you’ve been hacked is receiving unexpected password reset emails. A cybercriminal may be looking for information about your banks, shopping sites, and other services. Keep an eye out for emails, text messages, or
What to Do if Your Email is Hacked
Identity theft and bank account or credit card fraud are both possible consequences of a stolen email. If you suspect that your email has been hacked, act quickly to limit the harm for you and your email contacts.
Here are 9 steps to take if your email gets hacked to prevent the hacker from continuing their evil design and protect yourself in future attempts:
1. Change your email credentials
Create a new username and strong password for yourself. Your new password or passphrase should have at least 12 characters including numbers, symbols, and a mix of uppercase and lowercase letters. Each account should have its own password.
Consider changing your
Avoid questions with simple answers that can be easily guessed or found online. “What school did you go to?” is not a good example if this information is found on your social media profile.
2. Do a virus scan
Make sure you scan all the devices you use to access your emails. If the scan reveals malware, quarantine and remove it by following the
Install antivirus software that provides real-time protection against phishing attacks and dangers such as malware, ransomware, and other threats. Your PC, Mac,
3. Check your security settings
You should double-check the security settings on your account. Make sure your password recovery choices are current, and that your spam protection is turned on.
4. Alert your contacts
Notify your contacts that your email has been hacked and that any suspicious emails should not be opened or linked to any emails you’ve lately received.
Help stop the malware from spreading by telling your contacts not to click on the links and to be wary of any email you send that does not appear to be legitimate.
5. Check your mailbox settings
Even if everything appears to be in order, the hacker may have installed a filter or email forwarding tool. If so, they will be able to receive a duplicate of all your messages even if you are the only one who has access to the mailbox. Examine all mailbox settings, including those you might not think are relevant, such as any additional identities that have been added.
6. Check your other accounts
If your email was used to secure your other accounts, it’s critical to check that none of them was affected. We strongly advise that if you can log in, change your password to something more secure. Also, consider changing your email address. Implement
If you can’t access any of your accounts, change your password right away and call for assistance.
7. Restore your backup
The site files and emails are frequently backed up by web hosting providers. If this is the case, everything can be readily restored. Backups are not available by default if you use a business email provider. You’ll either have to manually download all of your emails every now and again, or you’ll have to pay for a third-party backup service

For example, Google provides this service for Gmail users. This is an excellent reason to keep your
8. Create an entirely new account
Unfortunately, despite your best efforts, you may not be able to restore access to your account. Creating a new email address or social network account is a last resort.
You should also verify if any of your other accounts were hacked as well. And this time, spend some time creating new accounts that are adequately protected.
9. Take additional security measures
If you would like to add an extra layer of protection, you can consider the following
- Secure your router and Wi-Fi
- Keep your operating system and apps up-to-date
- Install the latest version of
security software on all your devices - Use a
VPN on your computer and other devices - Avoid using public Wi-Fi
- Enable two factor authentication
- Don’t click on suspicious links and attachments in your email
Our final thoughts. There are no perfect solutions to email hacking. Email hackers are always finding new ways to infiltrate emails, but we hope that the tips we shared above may keep spam and hacking out of your inbox.
By entering your email address you agree to receive emails from EveryDayCyber. We'll respect your privacy and you can unsubscribe at any time.
Recommended Reading
What is a Computer Virus?
What's a computer virus? We hear about it all the time but do you really know what it is and how to prevent one?
BEST 10 Tips to Secure your Smart Home Devices
Smart devices are everywhere and rapidly becoming ubiquitous in our lives. Secure them or pay the price.
What is Two Factor Authentication
Two-factor authentication is a security mechanism in which individuals provide two authentication factors to log on to their account. Using a username and a password to log in to an account is in itself a 2FA. So is withdrawing cash from an ATM using your ATM card and a PIN.
Strong Passwords. One giant step to protect our digital lives
Here's how to create long, complex, and unique passwords to protect your accounts and keep your sensitive info safe from hackers.
What is an Ad Blocker?
An Ad Blocker is an app or browser extension that stops ads (popup, banner, inline) from displaying on your desktop or mobile device.
What is Smishing?
Smishing is a texting scam. Texts appear to come from reputable companies inducing you to reveal personal information, such as passwords or credit card numbers.