HTTPS and HTTP. We encounter these acronyms everyday as we surf the Internet.
But what are they and why should they matter?
What is HTTPS?
So what is HTTPS? HTTPS stands for HyperText Transfer Protocol Secure. It is an advanced and secure version of HTTP, or Hypertext Transfer Protocol. The “S” in HTTPS means “Secure”.
HTTPs enables web servers and web browsers to establish secure connections. It encrypts data being transmitted in both directions. This helps prevent thieves from stealing sensitive information along the way.
SSL transactions are negotiated using a key-based encryption method in the HTTPS protocol. The strength of this key is usually 40 to 128 bits.
For data communication, it uses port 443. It provides secure transactions by encrypting the entire text with SSL. It’s a hybrid of the SSL/TLS and HTTP protocols. It allows a network server to be identified in an encrypted and safe manner.
What is HTTP?
HTTP stands for HyperText Transfer Protocol. It’s the main method by which the data of web pages are transferred over the world wide web. Web pages are stored on servers and provided to client computers as the user requests them.
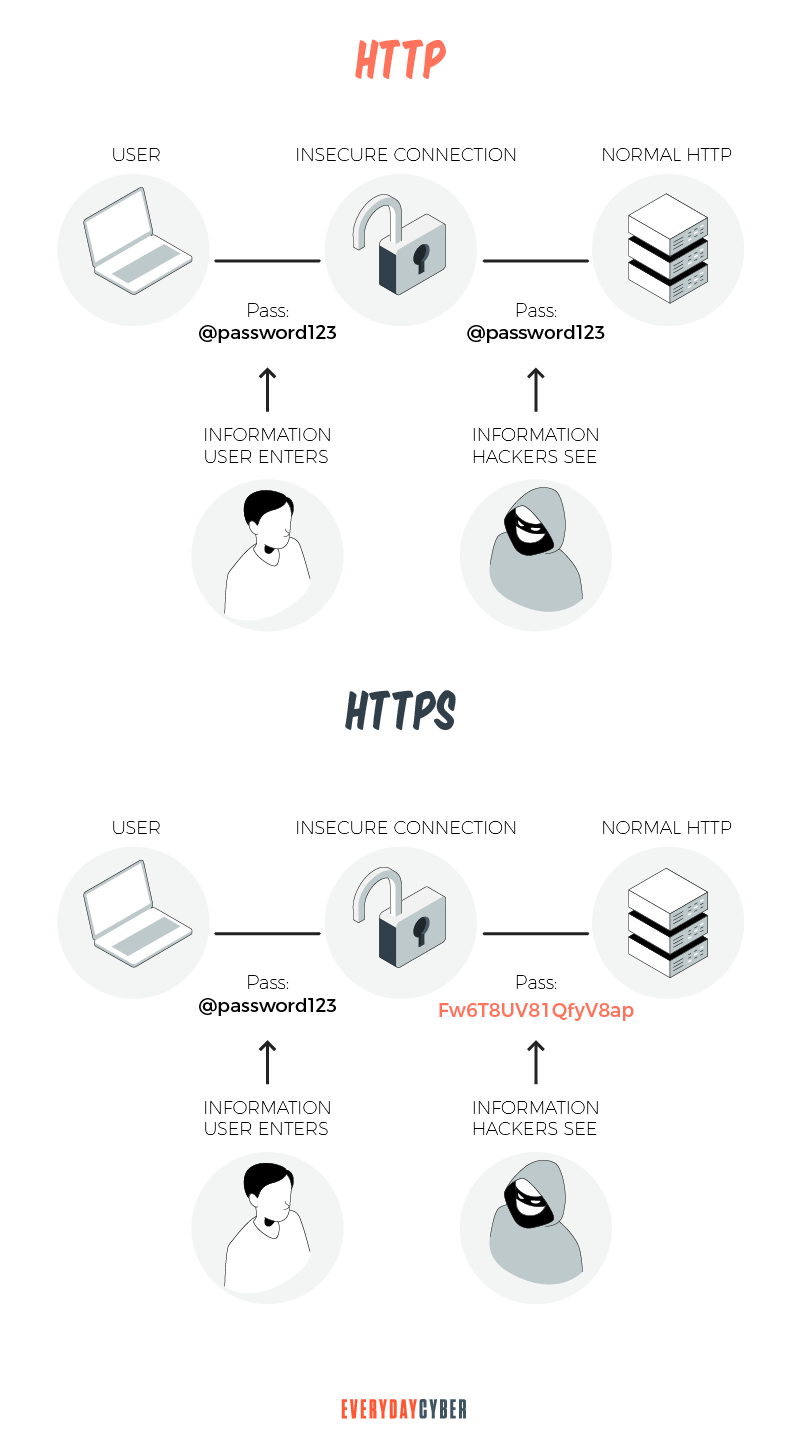
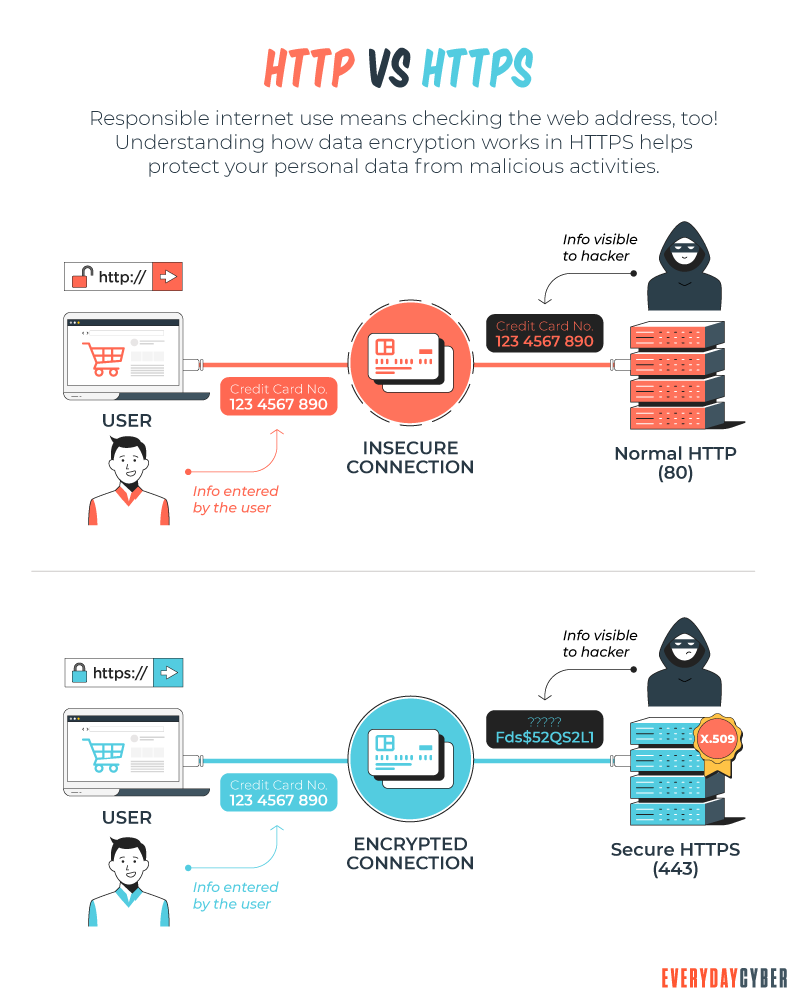
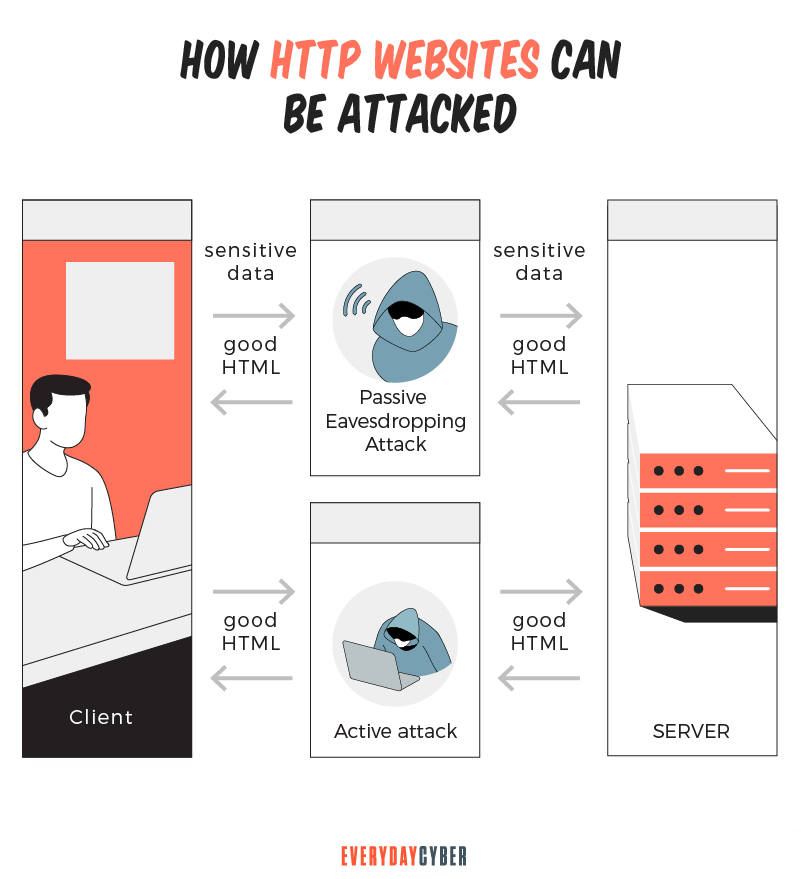
There is one major drawback to using a HyperText Transfer Protocol connection. Data exchanged through an HTTP connection is not encrypted. This puts your website in danger of third-party hackers obtaining your data. If you are on an HTTP page, any sensitive information should not be submitted.
By entering your email address you agree to receive emails from EveryDayCyber. We'll respect your privacy and you can unsubscribe at any time.
Differences between HTTPS and HTTP
Key Difference
HTTPS enhances the HTTP protocol by adding encryption, authentication, and verification. How?
Encryption
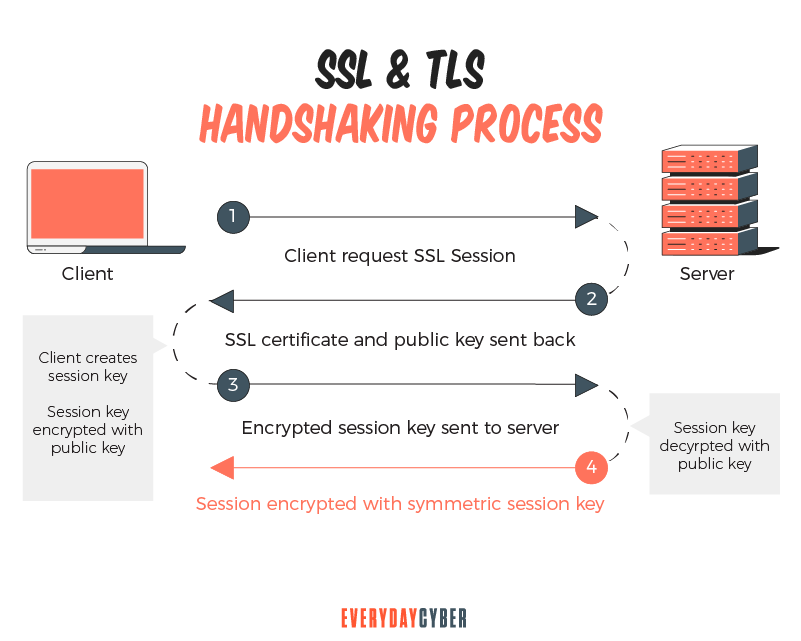
HTTP was initially built as a clear text protocol. As such, it is prone to eavesdropping and man in the middle attacks. HTTPS uses SSL/TLS encryption to protect data being transmitted over the Internet. Encryption helps prevent third parties from intercepting traveling information. SSL encryption works via a shared key using public-key cryptography and the SSL/TLS handshake. It establishes a secure connection between a web server and a web browser.
Authentication
HTTPS uses the SSL/TLS protocol to provide secure authentication. A website’s SSL/TLS certificate includes a public key. Web browsers use this key to certify that information from the server has been digitally signed by the holder of the private key. The browser will accept the certifying information if the server’s certificate has been signed by a trusted certificate authority (CA).
Verification
When an HTTPS web server transmits documents to a browser, it uses a digital signature. This signature verifies that a document has not been tampered with or corrupted during transmission. The server next generates an encrypted hash of the document’s content. The browser calculates independently to verify the document’s integrity.
Technical differences
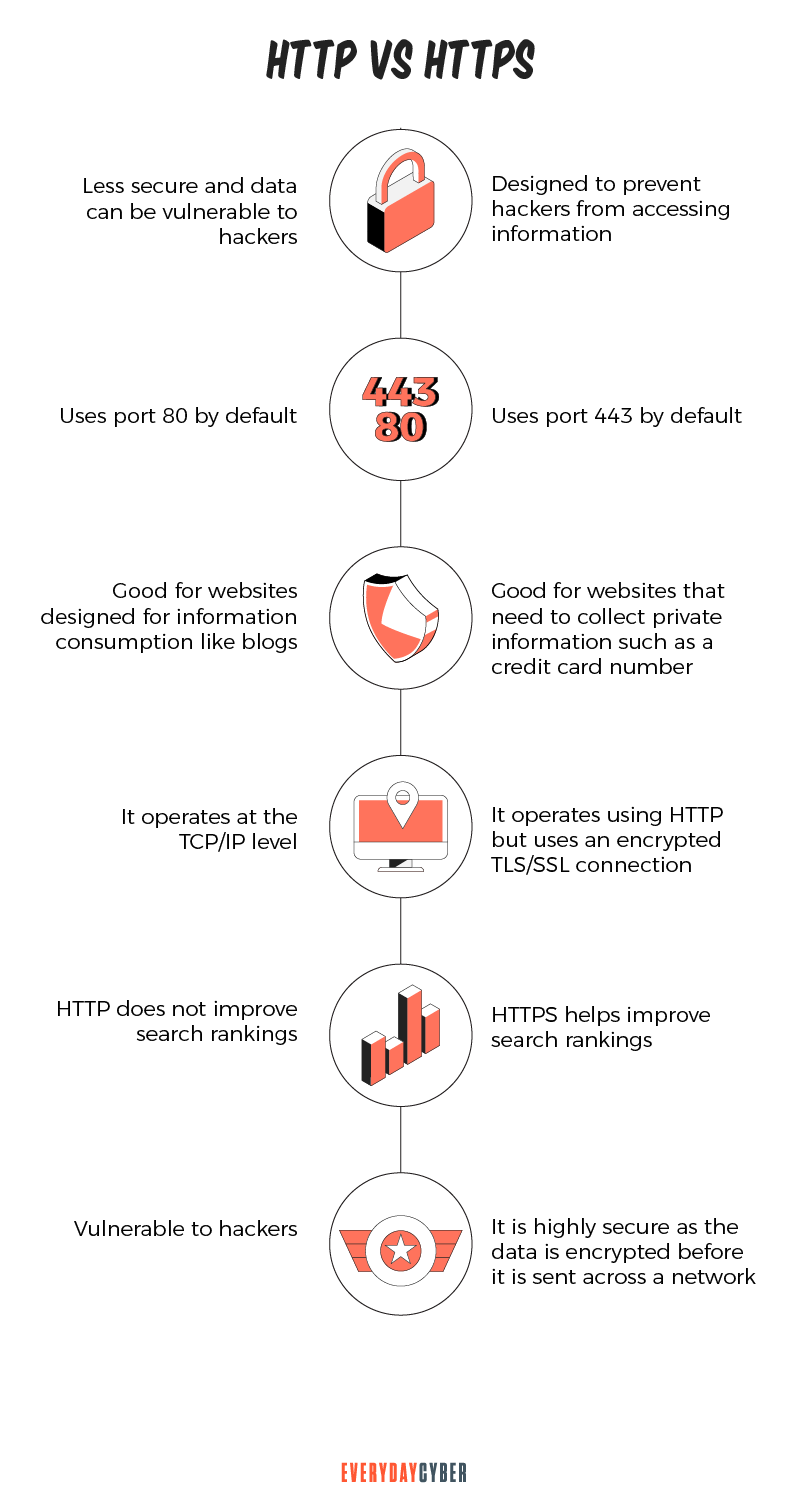
As to protocol
HTTP is a hypertext transfer protocol. It operates at TCP/IP level. HTTPs is a secured HTTP. It does not operate under a separate protocol but uses encrypted TLS/SSL connection.
As to encryption and security
HTTP websites don’t use encryption. They are less secure and more vulnerable to hackers. HTTPS websites use data encryption. They are highly secure against hackers who want to access critical information.
As to port
Port is used to let the computer know what kind of data is transmitted to or received from another machine over the same network connection. HTTP uses port 80 by default. Port 80 enables data transmission in plain text. HTTPS uses port 443 by default. Port 443 encrypts data packets before they are transmitted. By comparison, HTTPS is more secure than HTTP.
As to URL start
An HTTP address bar starts with http://. An HTTPS address bar starts with https://.

As to domain name validation
HTTP does not need SSL. HTTPS requires an SSL certificate.
As to speed
HTTP is faster than HTTPS because of its simplicity. HTTPS requires an additional SSL handshake phase. This extra step slows down the website’s page load time.
Why use HTTPS
There are a number of compelling reasons why you need to use HTTPS on your website. You’re better protected while surfing, buying, or working on the internet. Following are advantages of HTTPS that should convince you to use it.
Advantages of HTTPS
1. HTTPS protects your website
One of the most important advantages of HTTPS is data encryption. HTTPS constantly encrypts the data it sends and receives. As a result, the information is extremely safe. Even if hackers obtain those details, they will be unable to misuse them because the data has been encrypted.
No one can eavesdrop on sensitive information sent over an HTTPS connection. HTTPS is what allows for safe online banking and shopping. Unlike HTTP, HTTPS does not save any user data on the client system. As a result, the data is not at risk of being stolen in a public place.
2. HTTPS builds trust
One of the most overlooked advantages of HTTPS is that it aids in building user trust. The green padlock that appears in the browser offers your users trust. They will feel confident that your site can process sensitive transactions free from snooping eyes. This also helps safeguard your brand reputation.
HTTPS is particularly useful in safekeeping credit card information, passwords, and personal information. This
3. Verification and domain name validation strengthen the security of your website
HTTPS requires a
If you operate an e-commerce website, domain validation can help protect your business. Your digital certificate will improve the
4. HTTPS helps in SEO
A secure HTTPS connection is one of Google’s ranking signals. A site with an HTTPS certificate will be ranked higher than one without one, all factors considered. Sites that deal with money transfers, usernames, and passwords should consider HTTPS.
Limitations of HTTPS
HTTPS is a strong technology for securing the Internet. It should be used by all websites for all traffic.
Even when correctly deployed, however, the functions of HTTPS remain limited. HTTPS is a requirement for secure browsing, but it comes with its own set of drawbacks. Continue reading to learn more about them.
1. Computing overhead slows performance
Web servers and web browsers incur additional computing overhead as a result of encryption and decryption. This can be a problem if your HTTPS connection is handling numerous HTTPS connections at the same time. This slows down your website because the response time is delayed.
2. Accessibility can be an issue
Some firewalls and proxy systems prevent HTTPS sites from being accessed. This can be both purposeful and unintentional. Administrators may forget to enable HTTPS access. But they can sometimes limit access on purpose as a
3. HTTPS is not immune from mixed content
Mixed content happens when HTML on an HTTP website loads over a secure HTTPS connection. Conversely, secure HTTPS content can load to an unsecured HTTP connection. This creates a mix-up of content. As a result, some web material is loaded securely while others are loaded insecurely.
Why is mixed content dangerous? When a webpage has mixed or unsafe content, the entire website is exposed to
How HTTPS works
To encrypt communications, HTTPS employs an encryption protocol. The protocol is known as Transport Layer
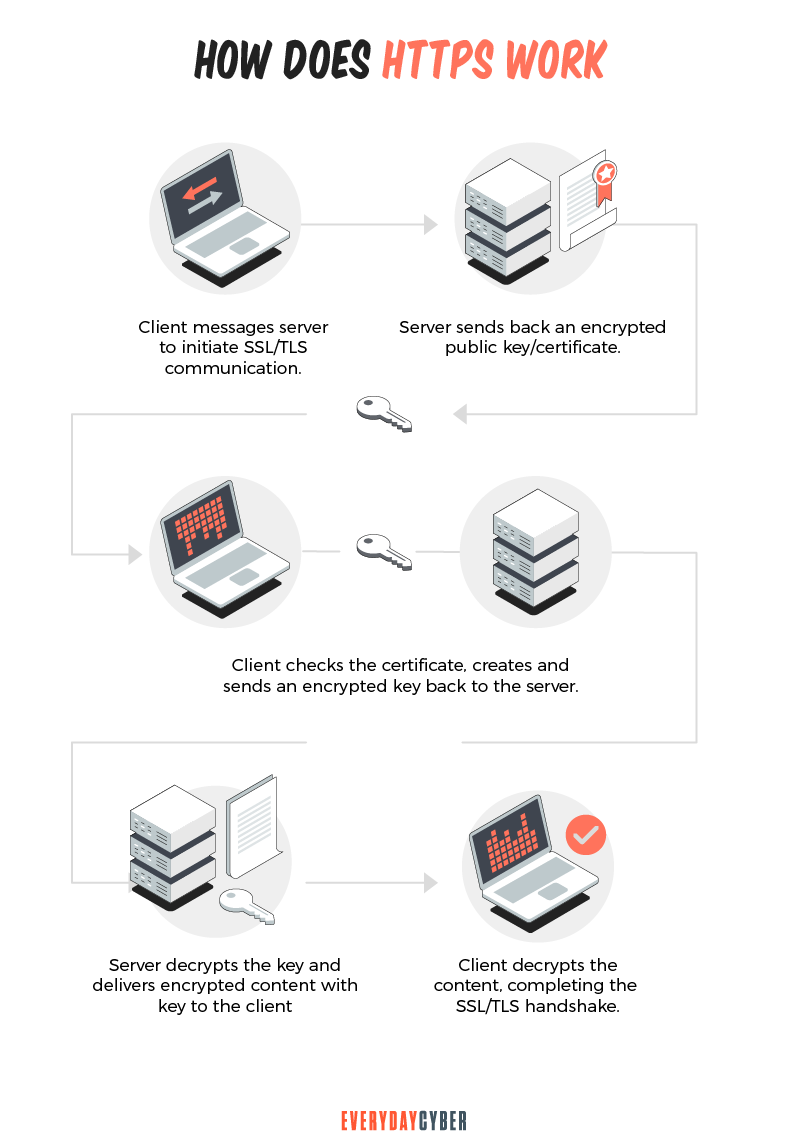
This type of
- The private key is owned by the website’s owner and is kept confidential. This key is stored on a web server. It decrypts data that has been encrypted using the public key.
- The public key is accessible to anyone who wishes to interact with the server in a secure manner. Only the private key can decrypt information encrypted with the public key.
TLS/SSL has two main functions:
- Checking to see if you’re talking to the server you think you’re talking to
- Making sure that only the server can read what you send it and that only you can read what it sends back
How HTTPS helps SEO
Lightweight ranking signal
In order to rank websites in search results, Google uses hundreds of signals in its algorithm. One of them is HTTPS. However, Google considers it as an insignificant ranking factor. Backlinks, content, and meta data are the major algorithmic signals. They will continue to be the most crucial SEO methods.
The HTTPS protocol is more of a “tie-breaker”. It has a lower SEO impact when compared to the major algorithmic signals. However, if all other elements are equal, it can be an advantage over the competition.
Website traffic
More traffic can result from higher rankings. More people noticing your site means more visitors for your site. Searchers may consider a secure site as a sign of confidence and authority. They would choose that site over a non-secure one, increasing your site’s click-through rate.
Conversions
Users trust secure connections more. HTTPS sites are more likely to rank better in Google search results. According to GlobalSign, 84% of users would cancel a purchase if data was delivered over an insecure connection. A sizable 85% would never visit an unprotected website.
What happens if my website doesn’t use HTTPS?
When you use HTTP, the information on your website is broken down into packets of data. These data packets are not encrypted. In fact, HTTP uses plain text for all communications. Plain text can be easily “sniffed” with free software. As a result, communication via an insecure public Wi-Fi network is vulnerable to
If you use HTTPS, intercepted data packets will appear as random characters. Encryption of information in transit makes this possible.
If you don’t use HTTPS, third parties can inject content into your web pages without your permission. This is usually in the form of advertising from an Internet service provider (ISP) aiming to boost revenue. They might place paid advertisements on your website. The earnings from the adverts are not shared with you when this happens. This can also compromise content quality. HTTPS prevents this from happening.
SSL/TLS certificates used with HTTPS
HTTPS encryption establishes a secure connection between a browser and a web server. It ensures that the interactions are secure. Website owners need website certificates to establish this secure connection.
An SSL/TLS certificate is used to verify the
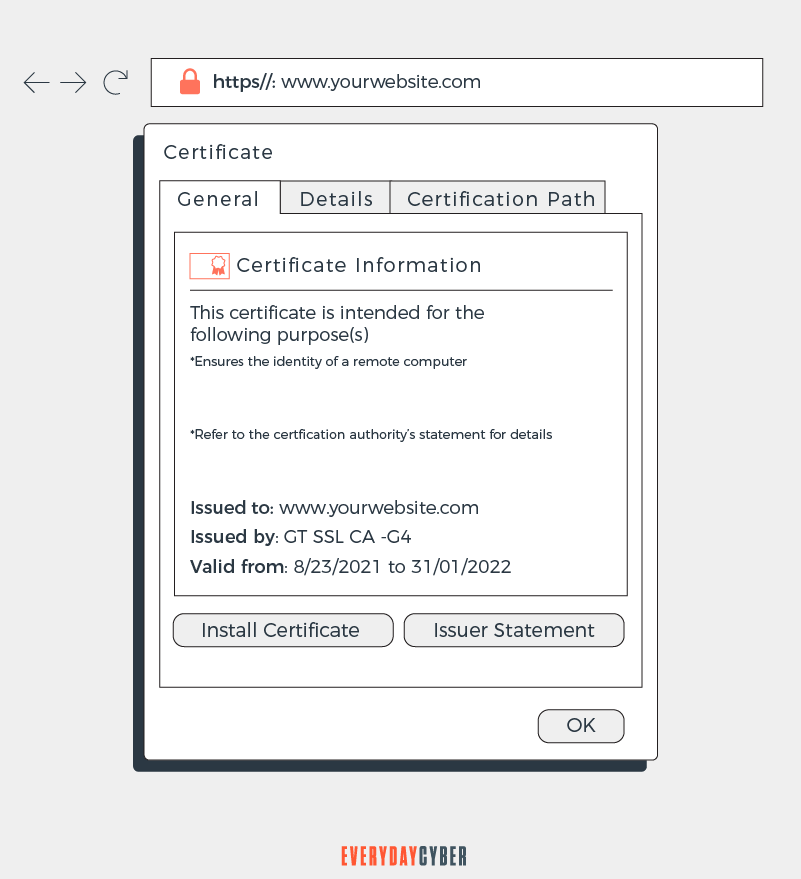
An SSL/TLS certificate contains the following:
- The public key of the website
- The domain name
- The digital signature of the issuing certificate authority
- Other critical information depending on the type of SSL
Types of SSL/TLS certificates
Single domain certificate
A single domain certificate is used for a single domain only. It can’t be used to verify any other domain, not even subdomains of the main domain.
Wildcard certificate
A wildcard certificate covers a single domain and all of its subdomains. A subdomain is part of the main domain. Subdomains usually have addresses that start with something other than ‘www.’
Multi domain certificate
A multi domain certificate (MDC) identifies numerous domains under a single certificate. Domains that are not subdomains of each other can share a certificate with an MDC.
Levels of SSL Certificates
Before a certificate authority (CA) gives an SSL certificate to a company, the company must be validated. The CA first verifies that the company owns and operates the domain.
The levels of validation range from the absolute minimum to extensive background checks. The distinction lies in the level of validation.
Domain validation
The least demanding level of validation is domain validation. A company has to prove domain ownership to receive an SSL certificate. The procedure is usually automated. This is the cheapest level of validation. It’s a good option for small businesses that want to get HTTPS.
Organization validation
Organization validation is a manual vetting process. The CA contacts the organization requesting the SSL certificate to gather company information. Organization validation certificates will show the company’s name and address. This information makes them more trustworthy for users than domain validation certificates.
Extended validation
Extended validation involves a thorough investigation of the company’s history. The CA verifies that the organization is lawfully registered as a business. Extended validation SSL certificates take the longest to validate. They also cost the most. But they are more trustworthy than other types of SSL certificates.
Large businesses, financial institutions, and online stores need extended validation certificates. They are ideal for websites that handle sensitive client information like passwords, credit card data, or names and addresses.
Our final thoughts: Secure sites are becoming the standard. The Internet is an open platform where bad actors love to roam. They will jump at every opportunity to do harm. HTTPS is your best bet for protection from hackers, phishers, whalers, and all sorts of cyber criminals. Aside from protection, HTTPS also helps build user trust and brand reputation. This is why HTTPS matters.
By entering your email address you agree to receive emails from EveryDayCyber. We'll respect your privacy and you can unsubscribe at any time.
Recommended Reading
Lock the Door. Bad Passwords: The Greatest Threats to Password Security
Bad passwords are the entry way for hackers to get into your accounts. Learn how to protect your cyber assets by using better passwords now.
What is Malvertising?
Malvertising is advertising malware that infects digital devices with malicious software using online ads and advertising networks as their delivery platforms.
14 Ways to Secure Your Home Wireless Network
Many homeowners are just unaware of the security threats that a wireless network might provide if not adequately safeguarded by a secure Wi-Fi network. We would never leave our house's front door unlocked. So you should do the same and never leave your Wi-Fi networks unprotected since it exposes you to the same or even worse threats.
What is a Rootkit?
Rootkits are nearly invisible and a dangerous type of malware that allows hackers access to computers without the knowledge of the owners. It is designed in such a way that it can remain in a network or on a computer system undetected for an extended period of time.
What is a Drive By Download?
A "drive by download" is a cyber attack where visiting a website or hovering over an Ad causes malware to infect your computer or device.
What is a Rogue Certificate?
A rogue certificate is a valid certificate issued by a legitimate certificate authority. However, it’s untrustworthy because either it was compromised or was issued to the wrong party.

