Adware can be frustrating, and almost everyone recognizes it when they experience it. That’s because it is first and foremost ANNOYING!!!! Popups and website redirections to places showing advertisements you had no intention of looking at. Bombarding you with crap that you have no interest in seeing and taking control of your desktop or

Adware is not always destructive. In the best case it is just immensely annoying. But more often than not it can be horrible, compromising your
So what can Adware do?
The real threat of Adware goes far beyond just displaying pop-up ads, changing your browser’s homepage, or redirecting your web browser to unwanted websites full of advertisements. It can be a nuisance and a severe threat, but it sometimes appears to be less threatening than say a ransomware popup. But here is the rub, Adware is often the tool bad actors and cybercriminals use to lure you into downloading even more dangerous malware.
Some of the direct ways Adware can affect your devices include:
- Infinite popups – Endless annoying popup ads that you seemingly can’t get rid of
- Spying – while not fully spyware, it can track your online activities especially what you do it through your browser
- Kill your performance – drains your device’s processing power by constantly downloading and loading ads
- Man in the middle attacks – is a particularly bad scenario because it redirects all of your internet traffic through a nefarious server including such connections you use to financial institutions like banks. Which means they can monitor and steal from those communications.
- Cost you money from excessive data – downloading images and videos displayed in the ads can be costly to your data charges.
How does Adware get on my device?
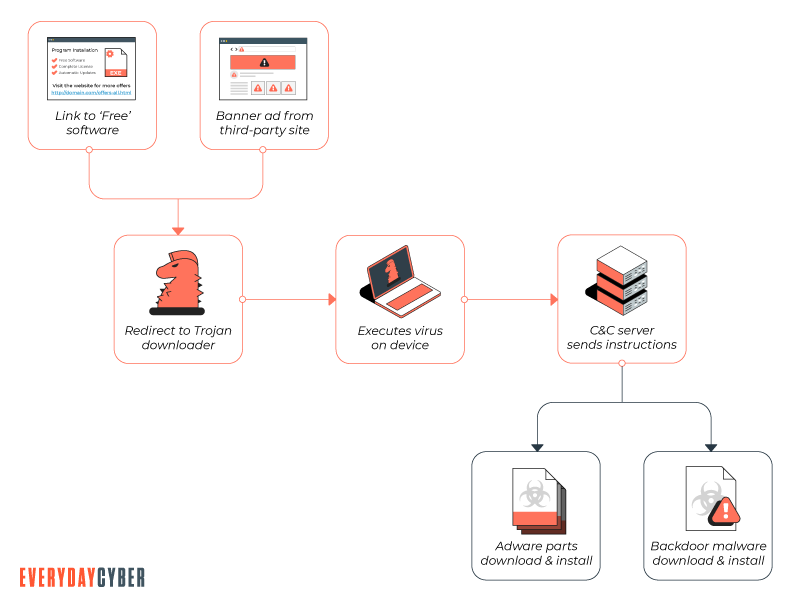
There are generally 2 ways Adware can get on your devices.
- You download an app, usually one that is free – Shareware or freeware – that contains the Adware. It gets installed without your knowledge as part of the free software.
- From an website. Some websites can be infected with Adware, which exploit vulnerabilities in your web browser to cause a drive-by download, resulting in more Adware or more sinister malware infecting your device.
By entering your email address you agree to receive emails from EveryDayCyber. We'll respect your privacy and you can unsubscribe at any time.
How do I know I am infected?
The most obvious one is the constant, annoying popups. But there are other indicators.
- Your device starts to get slower and slower
- Your device starts to crash for no apparent reason
- Your homepage for your browser changes – from google search to an Adware site
- Your internet connection gets slower and slower
Is it illegal?
Based on the nasty effects of Adware, you may be wondering, “is Adware illegal?”. The answer unfortunately is nuanced. The actual display of ads is not and in fact many of the free software apps, particular those used on

How to protect your devices from Adware.
The best strategy is the same as with all of malware, combine good cyber
Good practices include:
- Keep your software and operating system up to date
- Resist the bad actors attempts to lure you in with their slick ads and intriguing offers
- Keep you eyes peeled. Be suspicious of all websites, watch for fake websites and forged emails
- Check twice, click once. Do not trust any link that you are not 100% sure is safe. Assume all links go to bad places before clicking – it will save you a bunch of heartache.
- Do not download any file you are not 100% sure is safe and trustworthy.
Installing a quality antivirus/antimalware tool is still the best defense from all types of malware, there are some additional steps that can be done to prevent Adware infection.
Blocking certain kinds of scripts from running in your browser can help, Adware is usually written with the same programming language used by legitimate websites and services. But disabling these scripts does mean disabling the web as you know it.
There are also specific techniques and tools for the most common devices. See below for links to the most popular devices.
How to remove Adware on your PC.
How to remove Adware on your MAC.
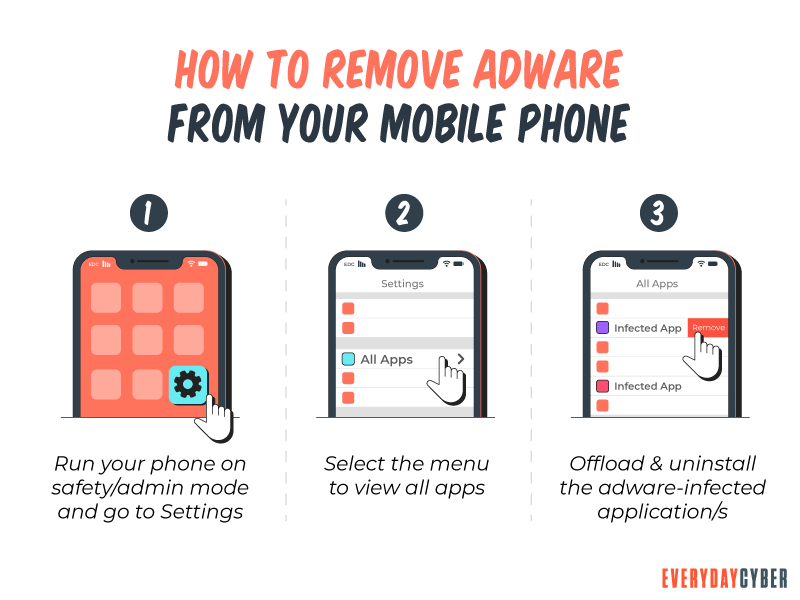
How to remove Adware on
How to remove Adware on IOS.
By entering your email address you agree to receive emails from EveryDayCyber. We'll respect your privacy and you can unsubscribe at any time.
Recommended Reading
What is a Potentially Unwanted Program (PUP)?
PUPs refer to programs, applications and other software downloaded onto computers or mobile devices that may have an adverse impact on user privacy or security. The term “potentially unwanted program” was coined by McAfee to distinguish the program from malware.
What is a Trojan Horse?
Trojan horse computer viruses are malware disguised as or hidden in legitimate software. Hidden from view and ready to attack.
What is a Rootkit?
Rootkits are nearly invisible and a dangerous type of malware that allows hackers access to computers without the knowledge of the owners. It is designed in such a way that it can remain in a network or on a computer system undetected for an extended period of time.
What is Spam?
Spam - spam emails, texts and sms messages (i.e. junk email), are unsolicited messages sent indiscriminately in bulk. Spam is a gigantic waste of time and resources.
What is Whaling?
Whale phishing is a targeted spear-phishing attack in which cybercriminals impersonate the high-level executives of an organization to send messages to lower-level company administrators in a position to do the acts being requested by the criminals on two things they want most -- money and data.
What is Two Factor Authentication
Two-factor authentication is a security mechanism in which individuals provide two authentication factors to log on to their account. Using a username and a password to log in to an account is in itself a 2FA. So is withdrawing cash from an ATM using your ATM card and a PIN.

