Virtual private networks (VPNs) are growing in popularity and usage worldwide. People use them in their homes, offices or businesses for a variety of reasons but mainly for privacy and security.
So what is a VPN
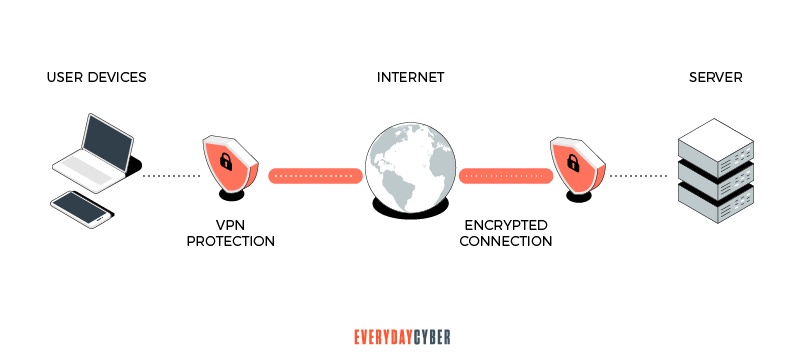
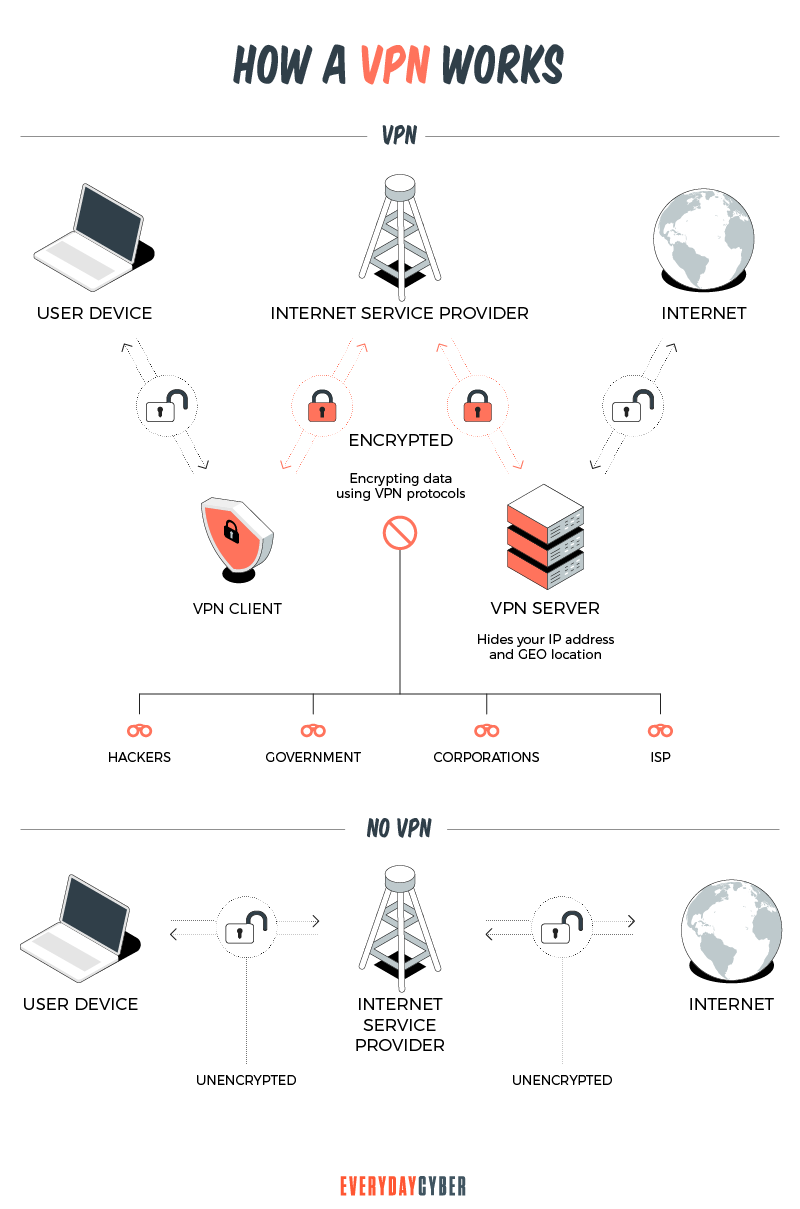
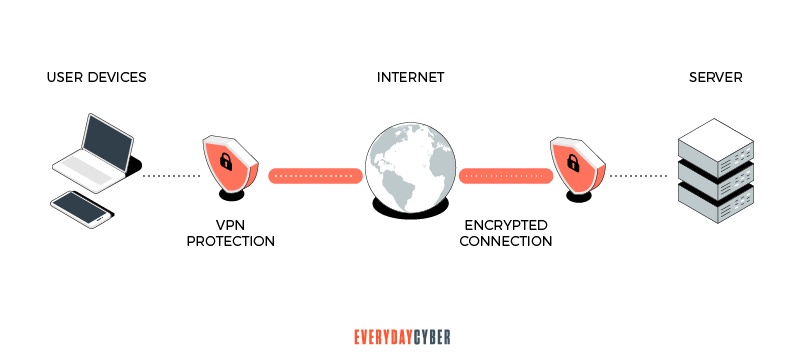
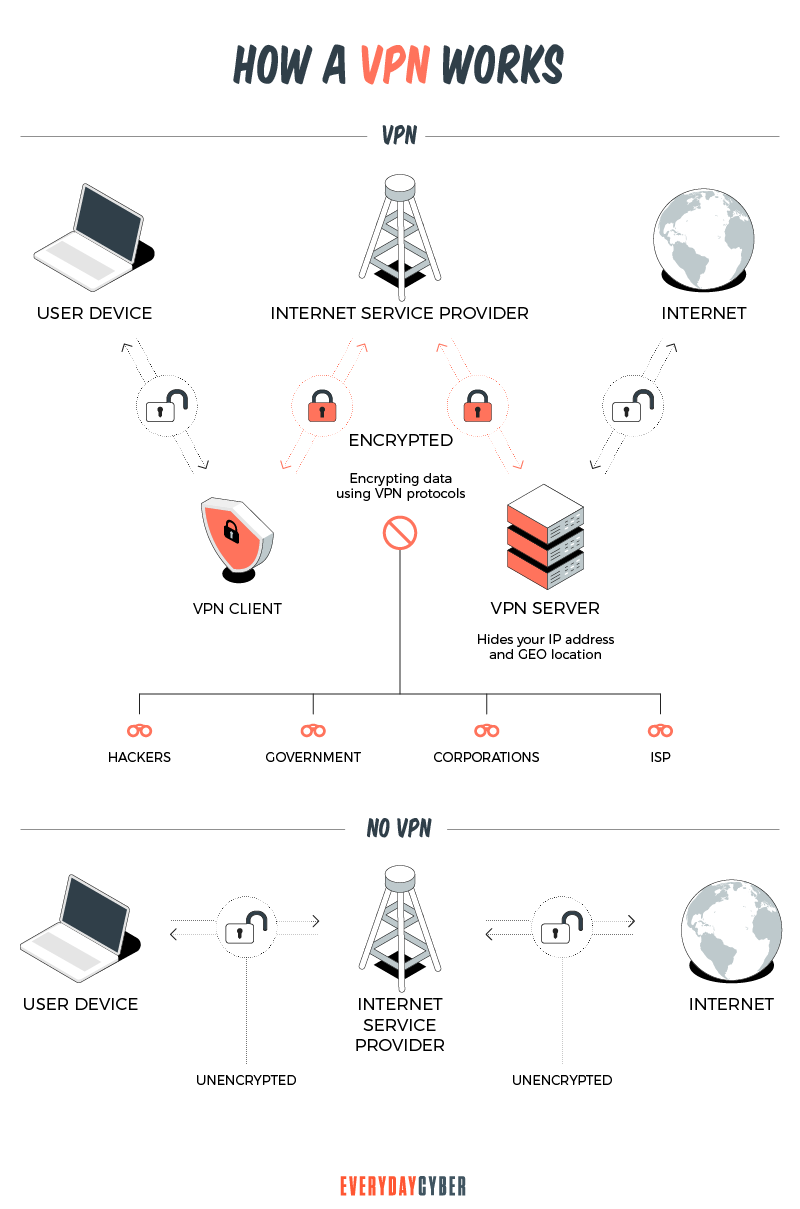
A VPN is a virtual private connection to a VPN host server to hide your identity, address and online activity when using a public Internet connection. It does this by encrypting your data and turning them into “rubbish” so no one can make sense of it even if they get their hands on it.
When you go to a website via the Internet, your computer connects to a remote private server which fetches the data you need from the Internet. The direct source of your data is the VPN server, not the Internet. This makes it almost impossible for third parties to track your activities online.
What does a VPN shield?
Since your connection is virtual, you are effectively out of the public eye when you use a VPN. Your VPN hides everything that identifies you to protect your privacy so you can enjoy the Internet without being tracked or surveilled..

Here they are:
Your IP address
Think of your IP address as your home address. Your home address leads people to your home while your IP address leads them to you and your devices. A VPN offers online privacy by encrypting your traffic to hide your identity. People attempting to track you or your activity will find themselves directed to your VPN host.

Your search history
Chances are your Internet Service Provider (ISP) has recorded the websites you have searched. A VPN can hide your browsing activities, like websites you have visited, search keywords and links clicked.
If you use a VPN each time you use the Internet, third parties trying to track you will only be able to see the IP address of the VPN host server. This prevents them from identifying your location, ISP and, potentially, sensitive information.
Your geolocation
Geolocation refers to the use of GPS, IP address or other location technologies to track the whereabouts of connected devices identifiable to their owners. A VPN “bluffs” online trackers into thinking you are in one place when you are in another.
For example, if you have a streaming service subscription and you are in another country, you can use your VPN to watch your favorite movies and games in your home country.
Your personally identifiable information
A VPN encrypts the data you send and receive to protect your personally identifiable information. This data may be your bank account, credit card, Social Security number or driver’s license. Using a VPN helps protect your personal information from the bad guys.
Your devices
Your devices may include your laptop, desk top, tablet and smartphone. They can be juicy targets for cyber criminals when you access a public Internet connection. A VPN helps protect the data you send and receive while you are on a public Wi-Fi.
What are VPN protocols?
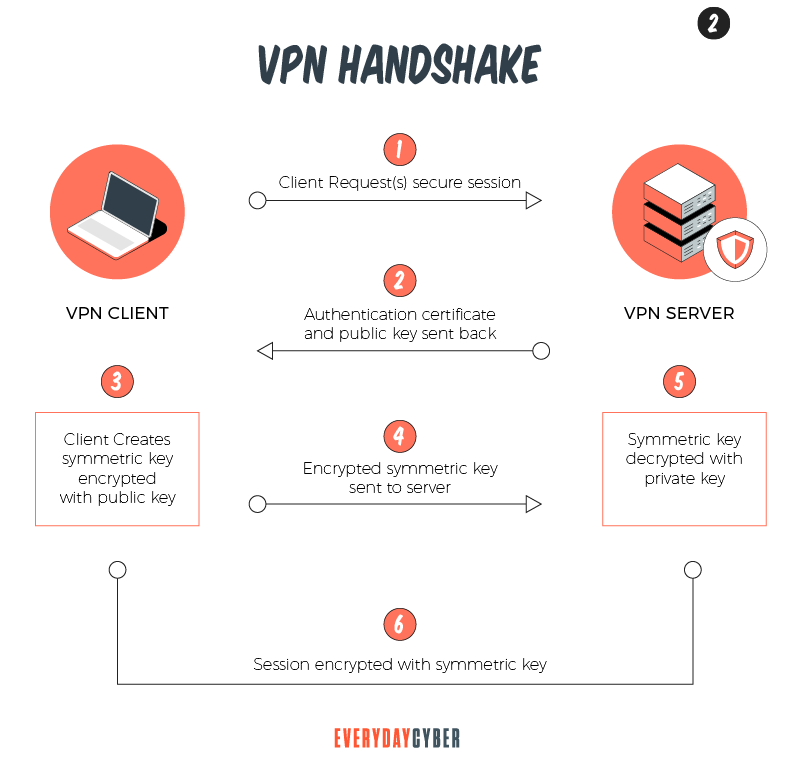
VPNs connect private networks and a public network, such as the Internet, by creating tunnels. VPN protocols determine how data moves in and out and around a connection. These protocols have different characteristics depending on the required goal. For example, some VPNs prioritize encrypting data for privacy and security while others focus on fast data throughput.
Following are common VPN protocols, the first three being the main types:
Secure Sockets Layer (SSL) VPN
The main focus of an SSL VPN is data security and privacy. It generally provides two things:
- Secure remote access via a web portal
- Network-level access between the client and corporate network
SSL VPN is commonly used by enterprises to connect departments and remote workplaces. It uses standard web browsers and and network technologies. Users can access enterprise applications without the need to install separate client software on each user’s computer. IT departments can also customize the required infrastructure services.
Site-to-Site VPN
A site-to-site VPN is a connection between two or more networks in an enterprise. It is a permanent encrypted link between offices. It is used by organizations that prioritize private, protected connections between their offices spread out over large geographical locations. These offices often have access to servers housed in a primary network to facilitate email and store data, as if they were located in their own physical facility.
For example, a company that has offices in New York, Los Angeles and Seattle can use a site-to-site VPN to exchange information. In effect, the VPN creates one whole network of remote offices communicating with each other with all data securely encrypted by the VPN
Client-to-Server VPN
A client-to-server VPN is a connection that provides employees access to the company network by first installing a VPN client. A VPN client is a software technology or application that is usually installed in a client computer to establish a secure connection to the main server. Many organizations have built-in VPN client capability pre installed on user devices.
A VPN client directly connects employees to company resources, bypassing third parties, including Internet service providers (ISPs). Employees can then use their computer or other digital devices at home to access applications related to their work and perform their tasks in a virtual environment.
Point-to-Point Tunneling Protocol (PPTP)
PPTP is one of the earliest VPN protocols, having been developed by Microsoft in the mid-90s. It provides a secure route of data from a remote client to a private enterprise network through a VPN over a public connection. It allows employees to securely access corporate resources without the ISP knowing it.
PPTPs offer lower costs on transmission, hardware and administrative overhead. It can also deliver one of the fastest connections for users who do not require heavy encryption.
Layer 2 Tunnel Protocol (L2TP)
L2TP is an extension of the PPTP protocol. It is a computer networking protocol provided by many ISPs to enable VPN services. It does not use native encryption but often uses the Internet Protocol security (IPSec) to provide security for data in transit.
IPSec is a set of protocols that authenticates all data communications over an IP network. It operates in two modes: the transport mode and the tunnel mode. When operating under the transport mode, IPSec prompts the source and destination hosts to perform all cryptographic functions. The tunnel mode uses special gateways to perform cryptographic processing in addition to the source and host destinations.
L2TP uses two tunnels: the voluntary tunnel and the compulsory tunnel. A voluntary tunnel allows the remote user to initiate the connection and sends the L2TP packets to the ISP which in turn sends them to the corporate network. In a compulsory tunnel, the remote VPN host initiates a connection to its ISP which establishes the connection between the remote user and the corporate network.
OpenVPN
An OpenVPN is an open source protocol that uses VPN functions to secure point-to-point and site-to-site connections. It helps to establish a secure channel between the VPN client and VPN server.
OpenVPN performs encryption and authentication via the OpenSSL library. This is a library for applications that secure communications over computer networks to protect the identity of the party at the other end.
OpenVPN uses either of two transport layer protocols to transmit data: the Transmission Control Protocol (TCP) and the User Datagram Protocol (UDP). TCP is a more secure protocol because it allows error correction and waits for confirmation before sending a new packet or sending a packet again. UDP does not perform error correction, allowing for faster transmission.
Secure Socket Tunneling Protocol (SSTP)
SSTP is a VPN protocol developed by Microsoft. It works by creating a tunnel between the VPN client and the VPN server, and encrypting all data and traffic that passes through the tunnel.
SSTP transmits point-to-point traffic and it does so through SSL/TLS channels. SSL or Secure Sockets Layer is the standard technology for keeping Internet connections secure. TLS or Transport Layer Security is an encryption protocol that provides end-to-end security of data sent between applications over the Internet. Since these two protocols provide encryption, secure key negotiation and traffic integrity checking, SSTP offers significantly more security than other VPNs.
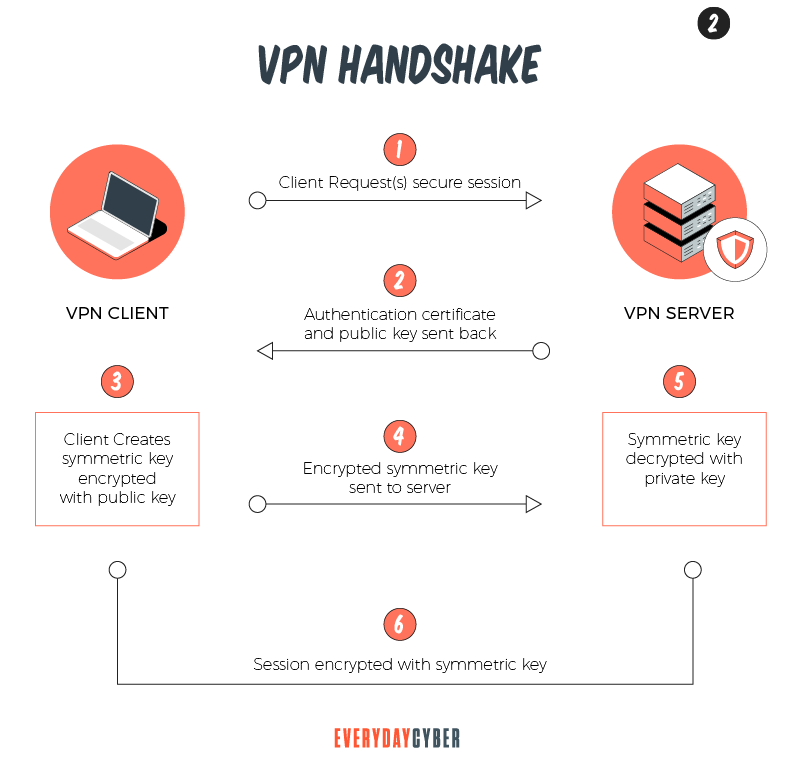
Internet Key Exchange version 2 (IKEv2)
IKEv2 is a VPN encryption protocol developed by Microsoft and Cisco. This protocol makes sure the traffic that passes through the tunnel between the VPN client and VPN server is secure by establishing the Security Association (SA) attribute within the application suite, such as IPSec. The SA attribute generates a symmetric key for both parties to encrypt and decrypt all data passing through the tunnel.
#2 So here we are at the middle of the post. We still think it's a good idea to signup.
By entering your email address you agree to receive emails from EveryDayCyber. We'll respect your privacy and you can unsubscribe at any time.
VPNs vs Proxy Servers
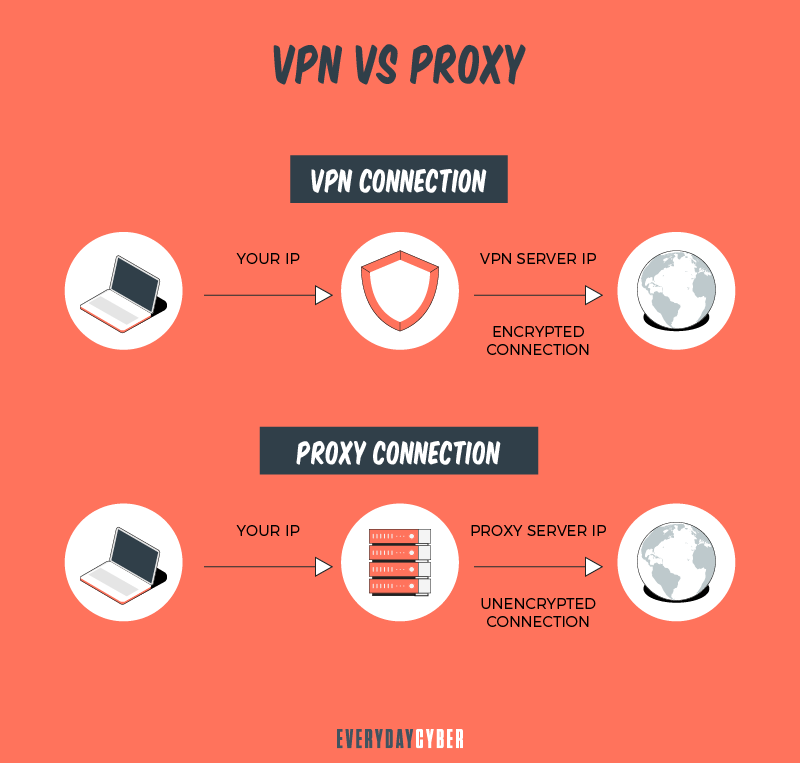
VPNs and proxy servers can help keep your activity private when browsing the internet, sending emails, streaming video, viewing social media and downloading files. But they operate differently and offer a user different values.
Proxy servers sit between you and the server or website you are trying to access, acting as a gateway to the internet. When you connect to a specific website, online service, or app from your computer, laptop, smart phone, or any other device, you first connect to the proxy server. The proxy server then modifies your source IP address and acts as if it was you when accessing services on the internet.
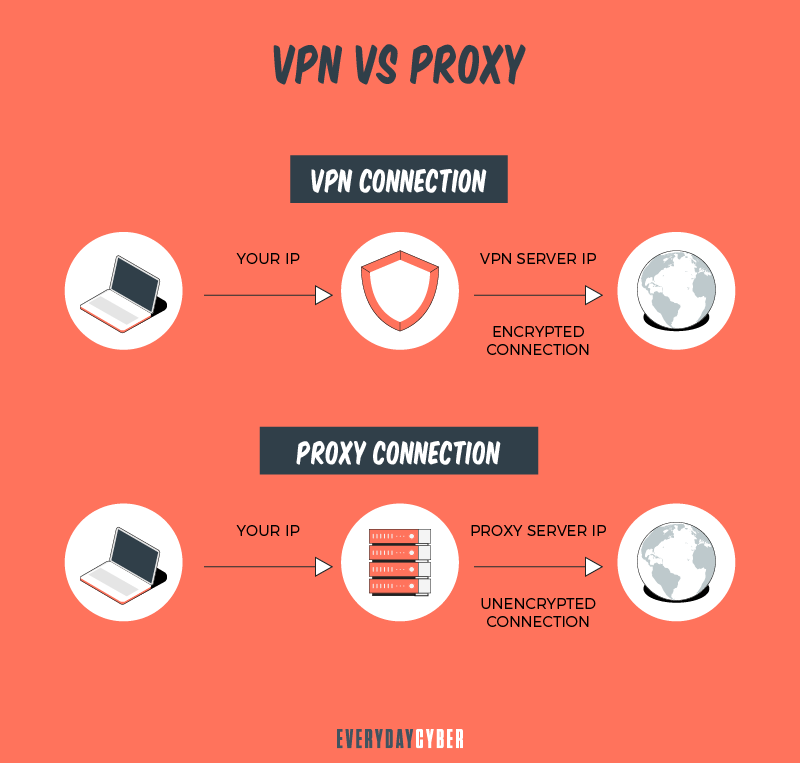
The benefit to this, is that you are able to hide your identity and even your real location. The website, app or online service only sees the IP address belonging to the proxy server. It won’t see your actual IP address. This will keep your identity and true location hidden from these sites and apps.
The three (3) the most common proxies are.
HTTP proxies
These proxies are used to access websites. They can also be used to access geo-restricted content because the IP address of the proxy server is in the correct geo-location for the service, even though your computer’s address is not. Keep in mind, this may violate the user agreement with your content provider so be aware.
SOCKS5 proxies
SOCKS5 proxies are generally used to access video streaming services, file-sharing sites, or online games. They don’t work with websites. SOCKS5 proxies, which are often free, are typically slower because free proxies generally have less configuration options, support, and slower infrastructure.
Transparent proxies
Transparent proxies are typically deployed by employers, parents, and public facilities like schools or libraries. The are intentionally transparent because the entity that set them up doesn’t really want you to know they are there. Typically they are enabled because there is a desire (limit restricted content) or need (regulatory) to filter user’s content when those users connect to the internet through their networks.
VPNs are similar to proxies, but they work with all access to external networks (internet) instead of just working with single apps or websites.
Like proxies, when you access a website after first logging into a VPN, your IP address is hidden and replaced with the IP address of your VPN provider. Like proxies, VPNs shield your identity and your real location. But unlike a proxy, this protection applies regardless of which websites you visit, online streaming sites you use, when you send emails or download files.
How VPNs and Proxies differ
1. VPNs encrypt your information
VPNs encrypt your traffic when you’re browsing and any data you send or receive, will be protected. This is important: It means that hackers, government agencies, businesses, or anyone else won’t be able to see what you’re doing when online. Proxy servers do not encrypt their traffic.
2. VPN providers promote online privacy
Most VPN providers have no-log policies. “No log” means the providers pledge not to track and store your online activity while you are using their service to connect to the internet. These providers won’t keep any data and so can’t sell information like what sites you browse or files you share to 3rd parties. Proxy servers, a particularly free proxy server operator may monitor traffic and sell your browsing data to third-parties.
3. Free proxy connections can be slower
Proxy servers and VPNs can slow down your browsing, depending on how many users are accessing their services. Free proxy connections are notoriously slow and often less secure because they have less support, offer less configuration options, and typically run on slower infrastructure.
4. You may spend more with a VPN
There are free VPNs. But using a VPN provider that charges a fee generally offers more privacy, more reliable performance and more secure connections. The true security of free VPNs can be and is often unreliable, as many providers use only one VPN method, called point-to-point tunneling protocol (PTTP), which is generally not secure. Paid VPN services offer high grade data encryption which is secure.
Do you need a proxy if you have a VPN?
The answer is “no”. VPN and proxy servers both mask your IP address. But a VPN will also encrypt the data you send and receive, something that a proxy server does not. If you are using a VPN, connecting to a website or app through a proxy server is an unnecessary step.
What to look for in a VPN
Choosing a VPN is like shopping for any product, such as a car or a dress. You have got to weigh the features, benefits and downsides, if any.

There are many differences between VPNs. It is your security and privacy that are at stake, so it is important that you apply significant due diligence when choosing a VPN.
Here are five things to consider when you buy a VPN:
1. Security and privacy
Obviously, these are what VPNs are for. You will want to be anonymous online and surf the web freely. Many VPNs boast of their amazing security features, but some are not enabled by default. Still others may work only in specific operating environments, such as the Windows version but not in the Android app, for example.
It pays to assess the features a VPN offers. So spend the time, read VPN reviews, consult colleagues or ask friends about their VPN experience. Investing some research time will pay dividends.
Following are some tips to remember when you are looking for a VPN that ensures your security and privacy:
Choose the best VPN protocol that suits your needs
The best VPN service providers will be very transparent about the security features of their services. They will offer high levels of encryption, strong protocols and other security features.
For example, the OpenVPN uses 256-bit encryption which is one of the best security levels for consumer VPN services. Not all operating systems support it but a good alternative is the IKEv2, which has a similar security profile.
Enable the kill switch by default
Many unexpected things can happen. A server can go down, for instance. If this happens and your VPN kill switch is not enabled by default, you go back to your unprotected Internet connection. The kill switch is a feature that will stop any data being sent to the Internet when your VPN connection fails.
Test for leaks
It is important that your VPN provider does not leak your domain name and IP address. If unchecked, these leaks can be seen and collected by your ISP or any other party that is able to access your network.
You can check if your provider has any DNS or IP leak problems by going to ipleak.net. You should also make sure that IPv6 is disabled to prevent your VPN provider from leaking your IP address to the Internet. IPv6 is the latest version of the Internet Protocol that identifies devices across the Internet, but most VPN providers do not support IPv6, so if it is enabled it most likely will only work outside the VPN environment.
Check the log policies
A trusted VPN service provider will not store identifying data. They can, however, log bandwidth usage, server load and server location to optimize provisioning of the service. Look for VPN providers that define their logging policies, and read and understand their private policy in full before signing up.
2. Speed
Of course, we all want a speedy connection without compromising security and privacy. There are times when a VPN server is overloaded due to high traffic. There are also VPNs that limit bandwidth.
Speed boils down to the quality, number and location of servers your VPN service provider offers. That is why it is worth investing in a quality VPN service. A larger number of servers means that the user should get more bandwidth, resulting in faster connections when using the VPN service. Server location is equally important and choosing the nearest server would give you the best and most responsive connection.
3. Ease of use and versatility
You don’t have to be a tech expert to use your virtual private network. Your chosen VPN should be intuitive and easy to operate.
Another factor you should look for in a VPN service is support for a variety of platforms and operating systems. An effective VPN will be able to make simultaneous connections to your laptop, PC and smartphone while leaving room for extra devices.
4. Strong encryption protocols
A VPN is only as secure as its encryption capabilities. Having a robust encryption protocol is the best way a VPN can secure your Internet traffic. Most VPN providers recommend the OpenVPN protocol for its security and flexibility. Another good option for Windows and mobile users is IKEv2.
Aside from keeping your identity, data, IP address and location hidden, a strong encryption protocol prevents your ISP from throttling your bandwidth since it cannot see what you are doing online. Encryption also fends off advertisers with spammy personalized ads who can collect your data to be later sold to other advertisers.
5. Around-the-clock customer service support
Customer service is important to VPN users to help them find their way around and make sure they get acquainted with the service quickly. This is especially true for new user. For existing users, top end customer service allows them to get answers and solutions to their problems in real time in case they experience issues with their VPN.
How much does a VPN cost?
The cheapest or most expensive may not always be the best. But definitely, you will want to get the best VPN services you need for your money. After all, your online security and privacy are valuable, so determining how much that value is worth is up to you. As they say, you get what you pay for.
VPN pricing depends on many factors, such as:
- Data usage volume
- Number of devices covered
- Number and types of security services
- Number, location and capabilities of servers you can connect to
- Length of contract
- And more
VPN prices can range from $10 to over $100 and most VPN services operate on a monthly subscription basis. If you are after the basic security features, VPNs at the lower end may be able to meet your needs. But if you want a higher level of security and more sophisticated features, you will have to weigh your options for the more advanced VPN services.
Free VPNs are available, but many experts say they rarely work. The risks and problems are way too many. For example, some free VPN services keep track of your online activities and may collect and sell your information. Some have security features that are just too weak, not to mention extremely slow connections. To get the best security features, you most likely will need a paid VPN.
In conclusion, hiding our identity and all the things we do on the Internet is an entirely reasonable concern considering the malicious forces out to encroach on our privacy. We can depend on a virtual private network to do this for us and making the right VPN choice is key to a secure and safe online experience.
#3 You really should sign up. "Scouts Promise" ... it really will help you stay cyber safe.
By entering your email address you agree to receive emails from EveryDayCyber. We'll respect your privacy and you can unsubscribe at any time.
Recommended Reading
What is a Trojan Horse?
Trojan horse computer viruses are malware disguised as or hidden in legitimate software. Hidden from view and ready to attack.
What is Phishing?
Phishing is a cyberattack that attempts to trick people using email, text messages, phone calls, or even fake websites into giving away sensitive and confidential information.
What is a Keylogger?
Keylogger is a digital surveillance tool. They can track every click, touch, key stroke, download and conversation carried out on the device they are installed on
What is an Ad Blocker?
An Ad Blocker is an app or browser extension that stops ads (popup, banner, inline) from displaying on your desktop or mobile device.
How to protect yourself from identity theft
Identity fraud is all over. Almost every day, we see news reports describing new techniques for crooks to steal your personal information, as well as warnings about big data breaches that expose your sensitive data to hackers on the Dark Web.
Element Chat Review: How Secure Is It, Really?
Element is a secure messaging app for safer personal and corporate communication and other group chats.