Rogue certificates are what they are – online mischief-makers roaming the Internet to wreak havoc to people and organizations.
Hackers have long tinkered with rogue certificates to carry on their evil intentions. They’ve targeted big companies and media organizations like Microsoft, Google, and Amazon. This is scary because we often visit these websites in our online lives.
Some alarming real-life attacks
In 2013, certificates issued by the French government’s CA “ANSSI” were discovered to be used for network interception. ANSSI was technically restricted to French territories.
In 2015, Google and Mozilla disapproved of China’s Internet Network Information Center CA (CNNIC) after it miss-issued certificates.
It’s not a new trend for PC manufacturers to put their own software on laptops and desktops. Dell began distributing its popular Inspiron and XPS laptops in 2015 with a rogue
eDellRoot is the name of the infamous certificate. It’s a
More recently in January 2021, Mimecast reported a digital certificate compromise. This digital certificate verifies and authenticates Mimecast’s services to the Microsoft Exchange and Microsoft Office 365 apps.
Attackers can use the stolen certificate to mimic reputable websites and deceive users into revealing personal information like passwords. If the private key is also stolen, they can eavesdrop on both client-server and server-client communication. Hackers can also use the stolen private key to sign malware and inject it into systems, while avoiding detection.
What is a rogue certificate?
Before we go deep into rogue certificates, let’s rehash our knowledge of digital certificates.
Digital certificate
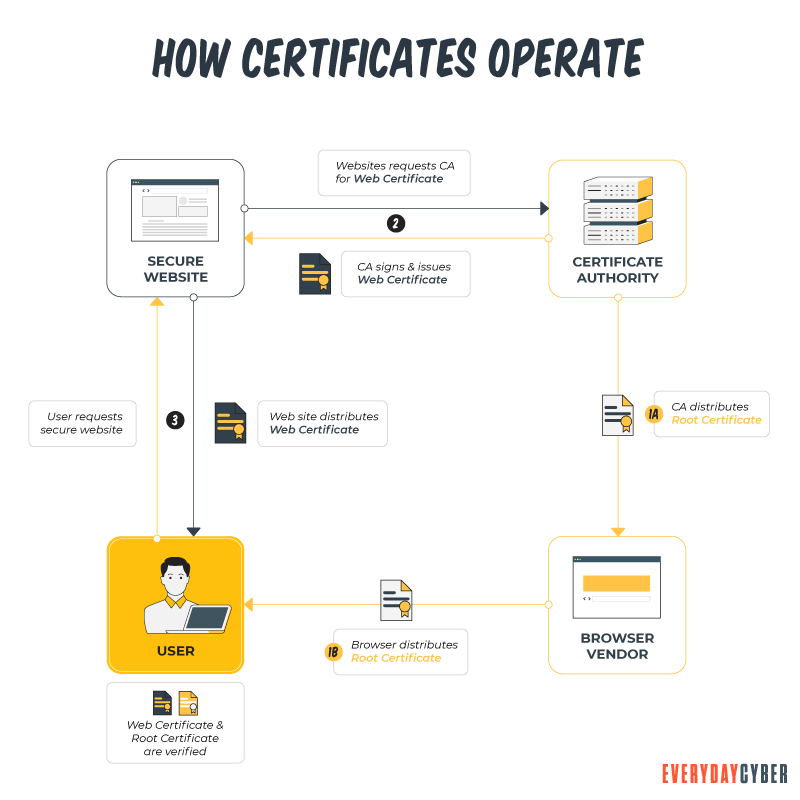
A digital certificate is a file or an electronic password that validates the legitimacy of a device, server, or user. The creation involves the use of cryptography in a public key infrastructure (PKI).
Organizations can employ website certificate authentication to ensure that only trustworthy devices and users are able to connect to their networks. Another common use of digital certificates is to confirm the authenticity of a website to a web browser. They are also known as secure sockets layer or SSL certificates.
A digital certificate contains identifiable information about the user. It may include the user’s name, company, and a device’s Internet Protocol (IP) address or serial number. A copy of the certificate holder’s public key is stored in a digital certificate. The public key must be matched to a corresponding private key in order to verify its authenticity.
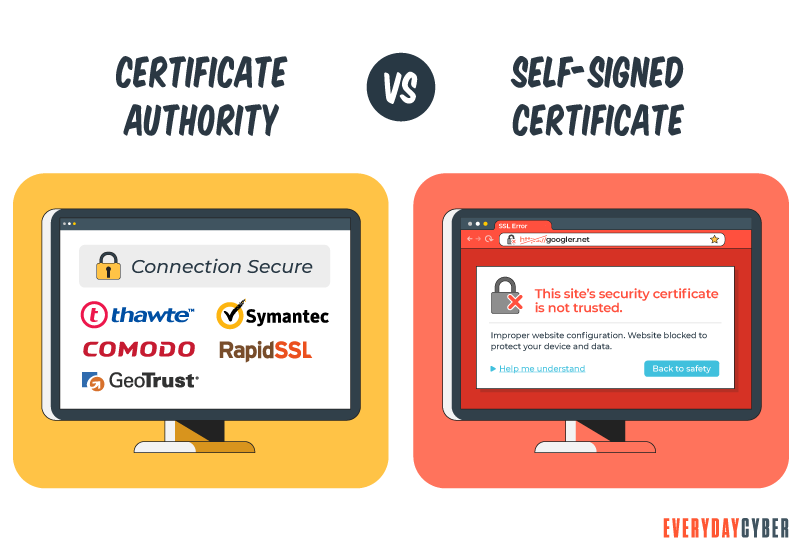
A certificate authority (CA) signs certificates to authenticate the
A certificate authority issues a certificate. It signs that certificate with one of its private keys. This private key may either be signed by a trusted root, or an intermediate root that was signed by the trusted root. Such a certificate is trusted as long as the certificate’s signature can be traced back to a root.
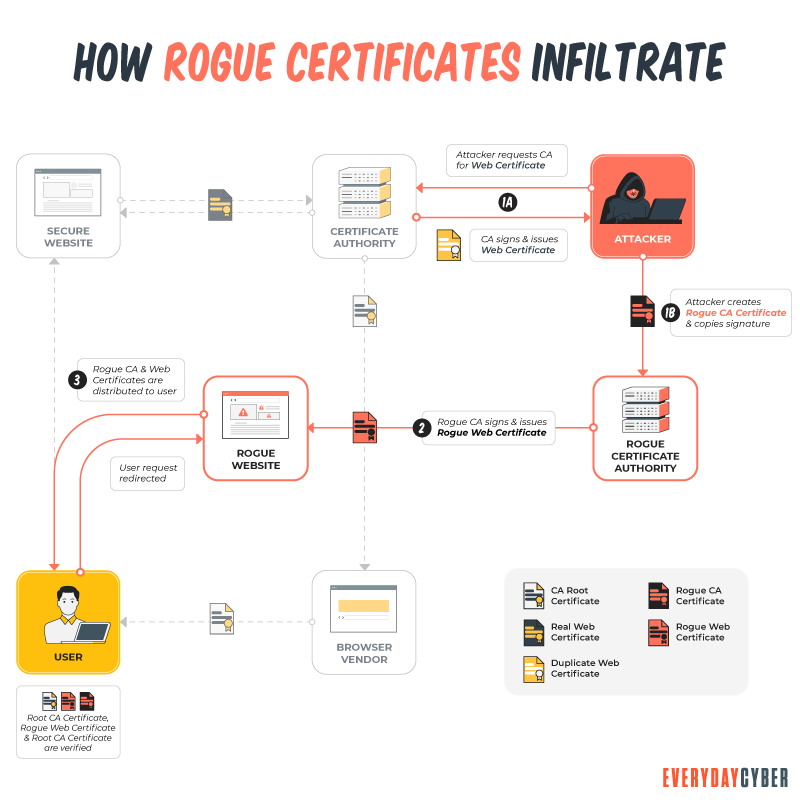
Rogue certificate
A rogue certificate is a valid certificate issued by a legitimate certificate authority. However, it’s untrustworthy because either it was compromised or was issued to the wrong party. A rogue certificate is a trusted certificate. This is why web browsers and users trust it. But it’s associated with a site that the certificate’s owner doesn’t actually control.
This is where the danger lies. Hackers could use a rogue certificate to victimize unsuspecting users. They could steal information,
By entering your email address you agree to receive emails from EveryDayCyber. We'll respect your privacy and you can unsubscribe at any time.
How are rogue certificates issued?
There are a number of ways an attacker can get a rogue certificate from a CA. They include:
Certificate authorities that go rogue
Rogue certificate authorities do exist. A certificate authority might go rogue for a variety of reasons. It could be as a result of a root compromise or deceitful management decisions. Or the CA might grant an intermediate root to a company that isn’t trustworthy.
Browsers immediately trust any endpoint certificate signed by trusted certificate authorities. They will also trust any certificate signed by the intermediate root because it was signed with a trusted root’s private key.
Breaching certificate authorities
Another way to get rogue certificates issued is to breach CAs. Attackers do this by:
- Impersonation – The attacker persuades the registration authority (RA) that he is someone else. That is, that he is the person permitted to request a certificate. An RA is the person in charge of ensuring that the person requesting a certificate is permitted to do so.
- Compromising the RA – The attacker gains access to the RA’s systems or an RA employee’s computer. Acting as the CA, the hacker issues a number of rogue certificates.
- Compromising the CA – It is possible for the attacker to get access to the CA’s systems and issue one or more rogue certificates. This is far more damaging than an RA attack since the attackers may be able to hide their tracks by tampering with logs. This makes it impossible to tell which rogue certificates were issued.
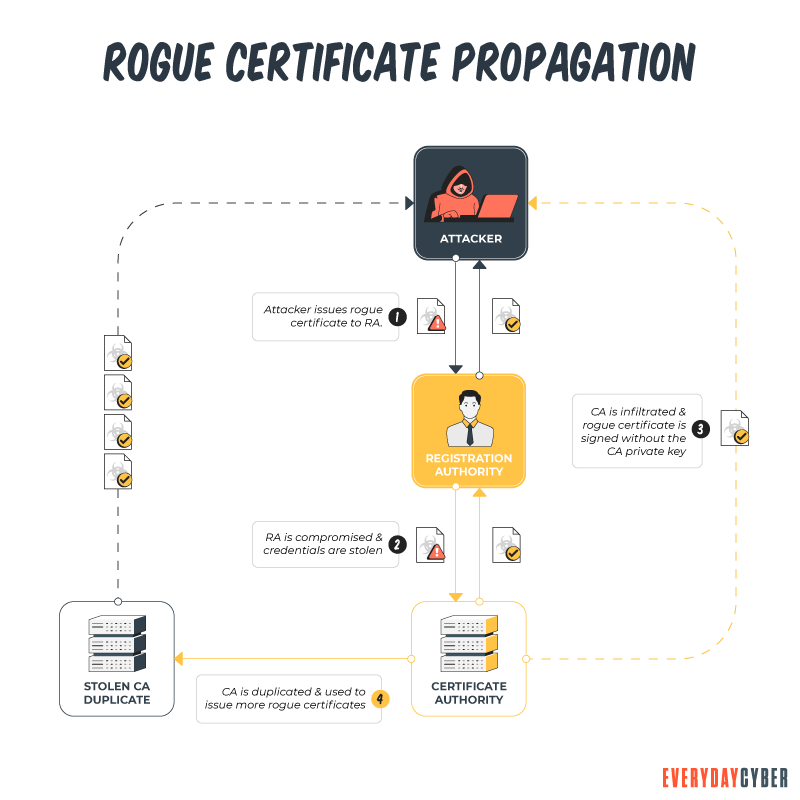
Stealing the private key of the CA
The hacker is able to get a copy the signing key of a trusted certificate authority. This allows the hacker to produce one or more rogue certificates. In this instance, the hacker will be able to choose when and how the rogue certificates would be issued and used.
Forging a certificate
The attacker exploits weaknesses in signing algorithms to forge one or more rogue certificates. The attacker can act as if he’s an employee of your company if the rogue certificate contains the name of one of your domains or workers. He can harm your company or your customers/partners in a variety of ways. All of your certificates may be affected if the compromised certificate authority is one you use to issue them.
Why is a rogue certificate dangerous?
Rogue certificates could be used by malicious systems to impersonate legit websites or create illegitimate sites. They could intercept and decrypt passwords, login cookies and other encrypted traffic destined for Google.
Rogue certificate authorities do issue valid certificates. These certificates can enhance the possibility of malware infiltrating your system. They are bad for your equipment because malware could destroy configurations and slow down systems.
How can you protect your company against rogue certificates?
The weakest points in the SSL ecosystem are rogue certificates. There are several actions you can take and useful industry resources you should consider to ease some of these worries. Here are some of them:
Certificate Authority Authorization (CAA)
Before a CA issues a certificate for a particular domain, it must validate that the requesting customer has control over the domain. Next, it checks the domain’s DNS CAA record to see if it is on the list of approved CAs. If the CA’s name is present, then it may issue the certificate.
Domain owners can identify the issuers of CAA certificates using an automated check provided by CAA. The CA may consider itself authorized to issue a certificate if it is on the white list. When CAA is completely implemented, rogue domain owners will be unable to shop for a lax CA.
In short, CAA allows you to restrict issuance of certificates for your domain by trusted certificate authorities only.
Certificate Transparency (CT)
CT is a way of informing domain owners about certificates that have been issued in their name. A CA stores information about each certificate request in at least one CT log. Domain owners can check CT logs directly. They may also use third-party monitors to look for certificates requested for their domain.
A token called a Signed Certificate Timestamp (SCT) is embedded in each certificate submitted into a CT log by the issuing CA. An SCT guarantees that the certificate request was successfully logged by the CA. This check will provide additional assurance that the CA took steps to notify domain owners of the certificate’s issuance. If there is no SCT, the browser should refuse to accept the certificate. It should also notify the user that the server is untrustworthy by displaying suitable visual warnings.
Best practices in certificate and key management
Good certificate management is a major deterrent of rogue certificate issuance. It pays to always go back to the basics, such as:
Gaining visibility
Continuous monitoring is the first line of defense in preventing digital certificate compromise. The monitoring tool should scan every certificate’s content. It should alert the
Remediating
After all of the certificates have been identified, the next step is to fix any weak points. This procedure should detect flaws such as weak keys or hashes. It should also be able to regulate the use of wildcard certificates and self-signed certificates.
Digital certificates and private keys must be kept in a secure location outside the network. This way, even if the system or network is compromised, the certificates and keys remain safe at all times.
Certificates that have expired should be renewed. Certificates that are weak or rogue must be removed from the certificate ecosystem.
Automating certificate and key management
One of the significant reasons behind certificate vulnerabilities is the human factor. Automating digital certificate processes helps avoid human errors.
The processes include certificate enrolment, provisioning, renewal, replacement, and revocation. Key management processes include key rotation and cryptographic algorithm upgrades.
Controlling user access
Many
You can do this through single sign-on, multi-factor authentication, privileged access control, governance, and other methods.
Continuous monitoring and scanning
To avoid outages and
The certificates should be checked for expiration dates. Keep an eye out for circumstances when they aren’t working, aren’t properly configured, or are vulnerable. The scan should also look for certifications that were created outside of standard protocols.
Any unusual behavior should be checked during the monitoring procedure. It should audit the certificate landscape on a regular basis to ensure that certificate policies are being followed.
Our final thoughts. You don’t have to be the victim of a rogue certificate attack to suffer serious consequences. For this reason, you must always be able to replace all of your certifications quickly and without causing any disruption.
None of these methods provide a comprehensive answer to the problem of incorrectly issued certificates. However, when widely used, either individually or in combination, they add to the arsenal of weapons used to safeguard secure websites.
By entering your email address you agree to receive emails from EveryDayCyber. We'll respect your privacy and you can unsubscribe at any time.
Recommended Reading
What is Encryption?
Encryption is the process of scrambling data – text, audio, video into an unreadable form, known as ciphertext, so only authorized resources can decode/access it.
What is a WPA2 Password
Your Wi-Fi password is the network security pass you use to connect to your home network. This password is important because it protects your system from intruders.
What is a Hacker?
A hacker is someone who challenges technology to see if it can be compromised. A hacker can black hat or white hat.
What is Scareware?
Scareware is rogue malware that preys on people’s emotions and fears, pressuring them to download unwanted software or click a link to avoid a catastrophe.
Strong Passwords. One giant step to protect our digital lives
Here's how to create long, complex, and unique passwords to protect your accounts and keep your sensitive info safe from hackers.
What is Ransomware?
Ransomware is particularly vicious malware that infects your digital device, encrypting your data and then holding you hostage until you pay a ransom.

