The Covid-19 pandemic that started in early 2020 not only transformed the way we all work. It has also opened the door for cyber criminals to target the new generation of remote workers. As a result, working from home is becoming a new entry point for cybercriminals looking to engage in various types of cybercrimes.

If you work from home, whether part-time or full-time, you must be aware of and protect yourself against
It’s easy to be complacent because home is a private space. We often forget that others may intrude into our exclusive space. Unfortunately, this is a reality that most remote workers face.
What Do the Figures Show?
People working from home carry most of their tasks online. They are more exposed to cyber attacks than ever before if they are not protected by the
Cyber criminals saw a great opportunity in the massive growth in working from home and the vulnerabilities of home office

UK-based data management company Databasix shares alarming survey results on home
- Since the end of February 2020, the number of phishing emails has increased by almost 600% as cybercriminals try to exploit the fear and uncertainty caused by the COVID-19 outbreak
- Antivirus software was not installed on employee devices in 68% of the organizations surveyed
- 44% of those polled stated they didn’t give their employees cybersecurity training on the dangers of working from home
- When asked why they fell for a phishing scam when working from home, 47% of home workers said it was because they were distracted
- Remote work has increased the average cost of a data breach by USD137,000
- In 20% of companies, remote workers caused
security breaches. - Email phishing attacks were the most common source of data breaches in home networks
- In April 2020, half a million Zoom user accounts were hacked and sold on the dark web
- In April 2020, Google blocked 18 million daily malware and phishing emails related to Coronavirus
Ways to Secure your Home Office
Working from home offers a huge amount of benefits in terms of convenience. But you can’t afford to let
In this blog, we’ve compiled seven ways to help you secure your home-based workplace and avoid the next cyber attack.
1. Start with your router
Your Internet router does far more than you might know. If your router’s settings are properly installed, it should have a firewall, wireless networking, and a variety of

If possible, set up your router in the center of your home or near your home office. This helps distribute network access more evenly. It’s also a good idea to place your router away from windows and external doors to protect it from prying eyes.
Remember that routers radiate horizontally, vertically, and diagonally. If you have a two-story home, locating your router on a high shelf on the lower level can ensure that both the upper and lower floors are covered.
2. Use strong passwords
There are many reasons to keep your passwords as strong as possible.
People can perform illegal activities on your network if your Wi-fi password is weak. If a hacker is able to access your network and do something illegal, you as the network owner are responsible for that activity unless you can prove that it wasn’t you – something that is difficult to do.
More concerning is the risk of giving away sensitive data that could be used by hackers to do evil things. The easiest way to avoid this occurring to you is to keep your network as safe as possible, so make sure your passwords are strong.

Weak passwords enable hackers to gain access to your files. If someone is able to easily get into your home office network, then they can easily get access to your local files. This gives them the chance to access confidential and sensitive information.
To prevent this from happening, make sure to use a strong Wi-Fi password. Another good practice is to disable network file sharing on your device.
Other people may also use up all of your bandwidth. Keep in mind that your available bandwidth is restricted. If people are able to easily access your WiFi network, a bunch of people may be using your Internet without you knowing it. This may result in slow download or streaming speeds. You can even be charged extra depending on your plan.
Related to strong passwords are secure passwords. A strong password is useless if you leave it where just about anyone could see it. Sadly, many people write their passwords on sticky notes attached to their computer screen.
Password Managers
One of the most secure ways to protect passwords is using

A password management solution will allow you to securely gain access to your data across all your devices, backup your data to the cloud automatically, and store sensitive accounts that contain credit card and banking information.
3. Use a VPN service
Using a virtual private network to safeguard data in transit is a good option to secure your home office. A
- Protecting the IP address of the user
- Encrypting data in transit
- Hiding the user’s location
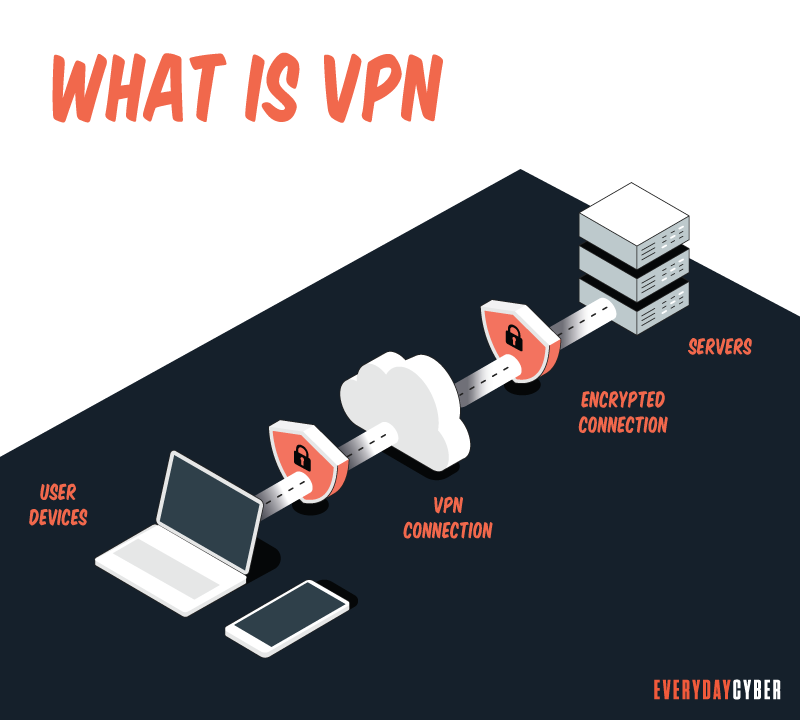
By using a VPN service on all of your devices, you hide your data by sending it to a third-party server through a secure tunnel, leaving hackers in the dark.
4. Use a firewall and antivirus software
Firewalls effectively function as a one-way digital barrier by preventing devices on the Internet from connecting to your network.
Network firewalls are enabled by default on most routers, so make sure yours is enabled as well. If your router does not have a firewall, you can install a reliable home firewall solution on your system.
Anti-virus software will help you avoid infections and will scan your computer on a regular basis to detect and clean up any problems.
5. Keep your software and devices updated
It’s crucial to keep your computer operating systems, such as Windows, iOS, or
This guideline should be applied to all the work and personal devices in your home network, including your wireless router, access points and extenders. Current updates will protect your network against existing and emerging threats.
6. Implement encryption (for both communications and work devices)
Encrypting email works similarly as a
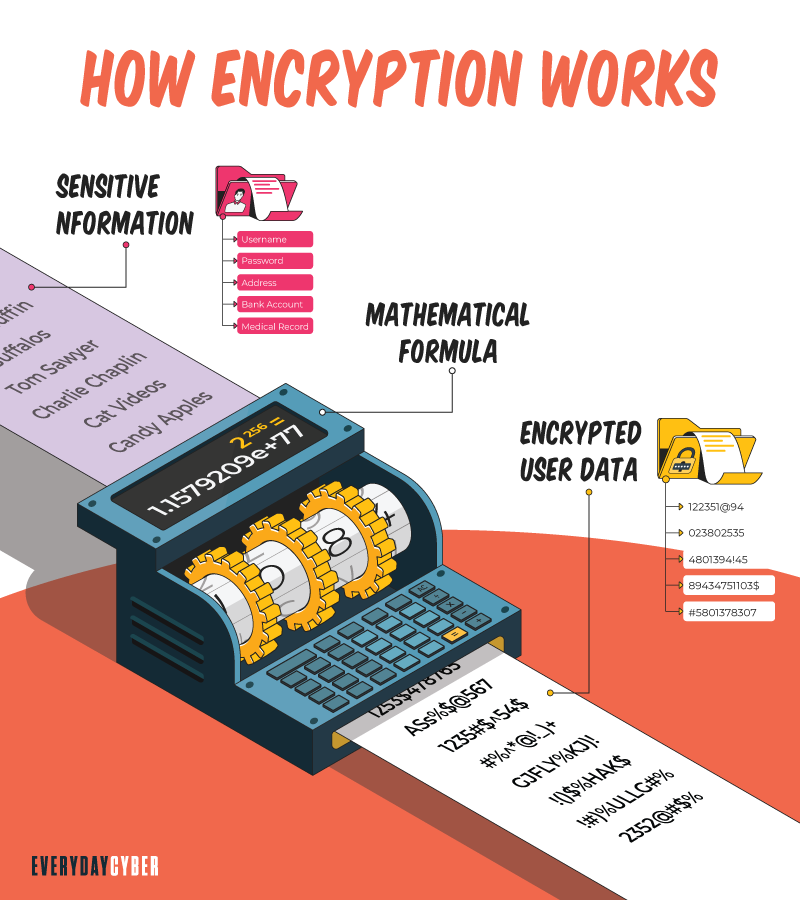
Device encryption protects your data on your hard drive by encrypting it. Only someone who possesses. Your files can be decrypted with the correct encryption key or a password.
7. Use two-factor authentication
When you’re working from home more frequently, you should enable two-factor or multi-factor authentication for critical websites.
2FA is an additional step added to the log-in process. Often, that extra step is a one-time code sent to your
2FA is especially useful for securing bank accounts. You’ll provide your login and password as usual when you connect into your bank’s website. Your bank, on the other hand, will send a code to your smartphone. Before you can access your online account, you’ll need to input this code.
Our final thoughts. Remote working looks like it’s here to stay, even after the pandemic. It’s all the more important to find ways to secure your home office work data and improve the overall
By entering your email address you agree to receive emails from EveryDayCyber. We'll respect your privacy and you can unsubscribe at any time.
Recommended Reading
What is Shoulder Surfing?
Shoulder surfing is a form of social engineering that enables cybercriminals to gather information just by looking over their victims’ shoulders. The aim of shoulder surfing is to obtain personal data, such as usernames, passwords or personal identification numbers (PINs), bank account numbers or credit card numbers.
What is a Password Manager?
A password manager is an encrypted storage system for keeping and managing passwords usually protected by a master password. Some password managers use biometric data to protect the vaults instead of master passwords. Still others support the use of two factor authentication for higher security.
Should you use a VPN?
The Internet can be a treacherous place. One of the most important measures you can take while online is to use a virtual private network (VPN), whether you’re at your workplace, on the go, or at home. VPNs keep your online activities secure and private, especially on public Wi-Fi. But VPNs can do so much more.
Why every small and medium business needs a cybersecurity strategy
A truck full of security studies show nearly every small businesses has exposed data and poor cybersecurity policies. Either build and execute a cybersecurity strategy or expect to be a victim of cyber crime. Be prepared, be proactive, and be safe.
What is a DDoS (Distributed Denial of Service) Attack?
DDoS attack or Distributed Denial of Service, is a coordinated attack intended to crash and make unavailable targeted websites and online systems by overwhelming them with data.
What is HTTPS?
HTTPs enables web servers and web browsers to establish secure connections. It encrypts data being transmitted in both directions. This helps prevent thieves from stealing sensitive information along the way.


